The 'Orphaned Asset' Vulnerability Window
There is a dangerous fallacy in private equity Value Creation Plans: the belief that you should leave an acquired company's technology stack alone for the first 12 months to avoid "culture shock." While this approach preserves operational velocity, it creates a massive security liability. In the 2024 threat landscape, the period immediately following deal closure is not a grace period; it is a target window. Recent data indicates that 68% of private equity portfolio companies report an increase in cyber incidents during the month of a deal closure.
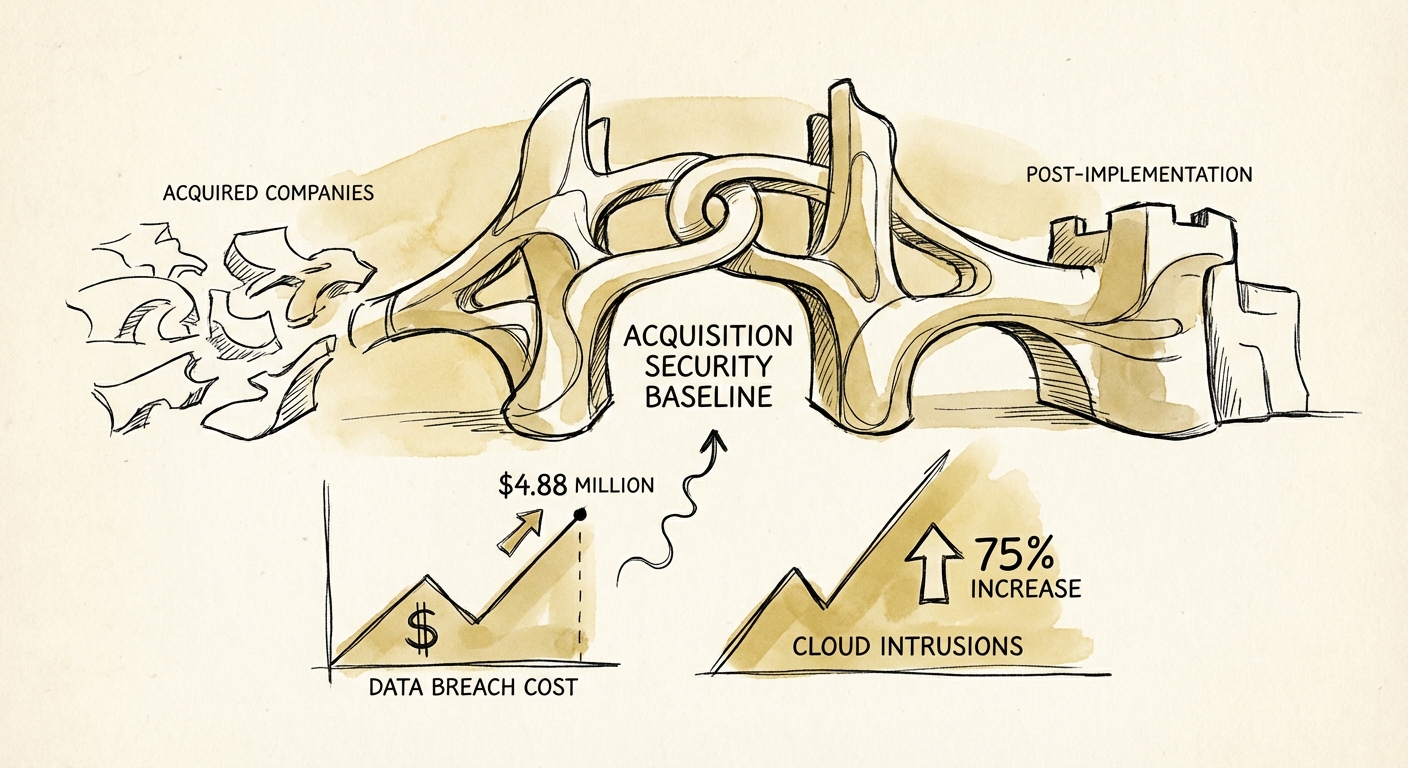
Attackers know that during the first 100 days, the acquired entity is effectively an "orphaned asset." It no longer has the focused attention of its founder (who has cashed out), but it does not yet have the protective infrastructure of the platform company or the PE firm's CISO. It exists in a limbo state—often with legacy credentials, unpatched vulnerabilities identified in diligence but not yet remediated, and employees distracted by integration anxiety.
The financial consequences of this gap are escalating. According to the IBM Cost of a Data Breach Report 2024, the global average cost of a data breach has reached $4.88 million, a 10% increase from the previous year. For PE firms, this isn't just an operational expense; it is a direct hit to EBITDA and a potential valuation killer if the breach exposes customer data or intellectual property during the hold period.
Defining the Private Equity MVSP (Minimum Viable Security Posture)
You cannot integrate an entire IT stack in 100 days, but you must enforce a security baseline. We call this the Private Equity Minimum Viable Security Posture (MVSP). This is not about full ISO 27001 compliance or SOC 2 readiness immediately; it is about closing the doors that allow 75% of cloud intrusions to occur, as reported in the CrowdStrike 2024 Global Threat Report.
The MVSP focuses on three non-negotiable controls that must be deployed within the first 30 days post-close, regardless of the underlying tech stack:
1. Identity Centralization (The "Kill Switch")
Identity-based attacks are the primary vector for modern breaches. If your acquired company is still managing access via spreadsheets and local Active Directory, you have zero visibility. Mandate: Federated SSO (Okta/Entra ID) for all critical SaaS apps (Salesforce, AWS, NetSuite) within 30 days. This gives you a single "kill switch" for offboarding.
2. Endpoint Visibility (The "Flight Recorder")
You cannot protect what you cannot see. Legacy antivirus is insufficient against ransomware. Mandate: Deploy a modern EDR agent (CrowdStrike/SentinelOne) to 100% of endpoints. This provides immediate telemetry and the ability to isolate infected machines remotely.
3. MFA Enforcement (The "Gatekeeper")
Password reuse is rampant in lower middle-market companies. Mandate: Enforce phishing-resistant MFA on all email and remote access points. No exceptions for executives.
The 'Overlay' Strategy: Standardize Without Integration
The most common pushback from Operating Partners is, "We don't have the budget to migrate them to our tenant yet." This is a false choice. You do not need to migrate a portfolio company's email or ERP to the parent company's tenant to secure it. You need to apply a Security Overlay.
A Security Overlay involves deploying your standard security toolset over the top of their existing infrastructure. You treat the acquired company as a hostile network until proven otherwise. This approach allows you to achieve risk reduction without the operational disruption of a full IT migration.
The 100-Day Security Roadmap
- Day 1-7: Deploy EDR to all endpoints. Gain visibility.
- Day 8-30: Federate Identity. Connect their Google Workspace/O365 to your IdP. Enforce MFA.
- Day 31-60: Conduct a "Purple Team" assessment to validate the new baseline against real-world attack vectors.
- Day 61-90: Remediation of critical technical debt identified in Diligence (e.g., patching public-facing servers).
By decoupling security standardization from IT integration, you protect the asset immediately while buying yourself time to plan the complex operational merger. In a market where breaches with lifecycles over 200 days cost $5.46 million, speed is your only hedge.