The 'Day 1' Identity Illusion: Where Deal Value Evaporates
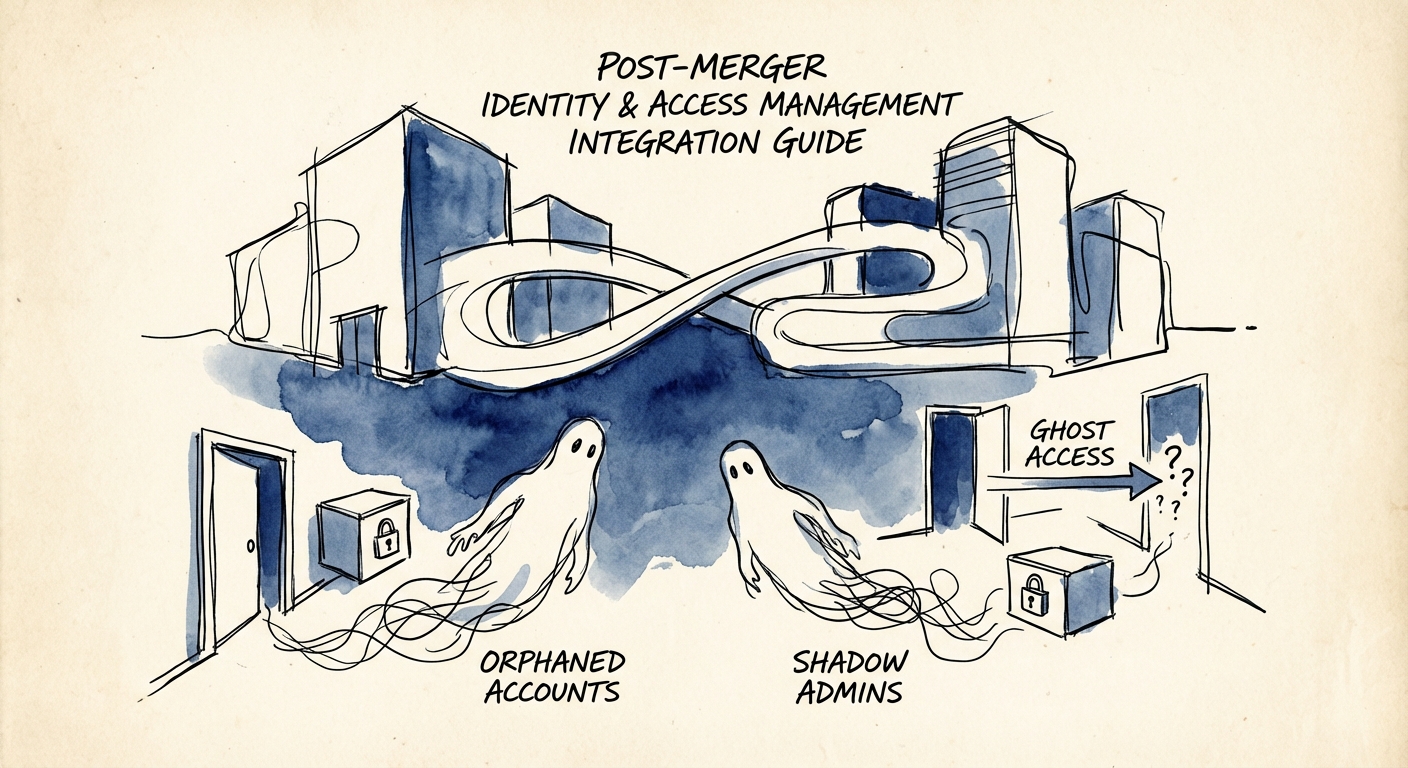
In the rush to achieve "Day 1" connectivity, Private Equity operating partners and CIOs often commit the cardinal sin of post-merger integration: they prioritize connection over consolidation. The standard playbook involves establishing a two-way trust between Active Directory (AD) forests or hastily federating Identity Providers (IdPs) to allow cross-entity email and file sharing. While this checks the operational box, it opens a massive security chasm known as the "Ghost Access" gap.
Recent data indicates that 33% of firms experience data breaches specifically attributed to M&A integration activity. This isn't a coincidence; it is a structural failure. When two distinct identity environments are bridged without rigorous hygiene, the acquiring entity inherits every dormant account, shadow admin, and weak password policy of the target. We call this "importing the breach." The target company’s "orphaned" accounts—VPN credentials for contractors fired six months ago or service accounts with domain admin privileges—suddenly have a pathway into the parent company’s crown jewels.
Consider the cautionary tale of the Yahoo acquisition, where undisclosed breaches led to a $350 million valuation haircut. In the mid-market, the numbers are smaller but the impact is often fatal to the investment thesis. If your "Day 1" strategy relies solely on AD trusts without a comprehensive audit of who is being trusted, you aren't integrating a company; you are integrating its vulnerabilities. The goal of IAM integration must shift from "enabling access" to "verifying identity," treating the acquired environment as hostile until proven otherwise.
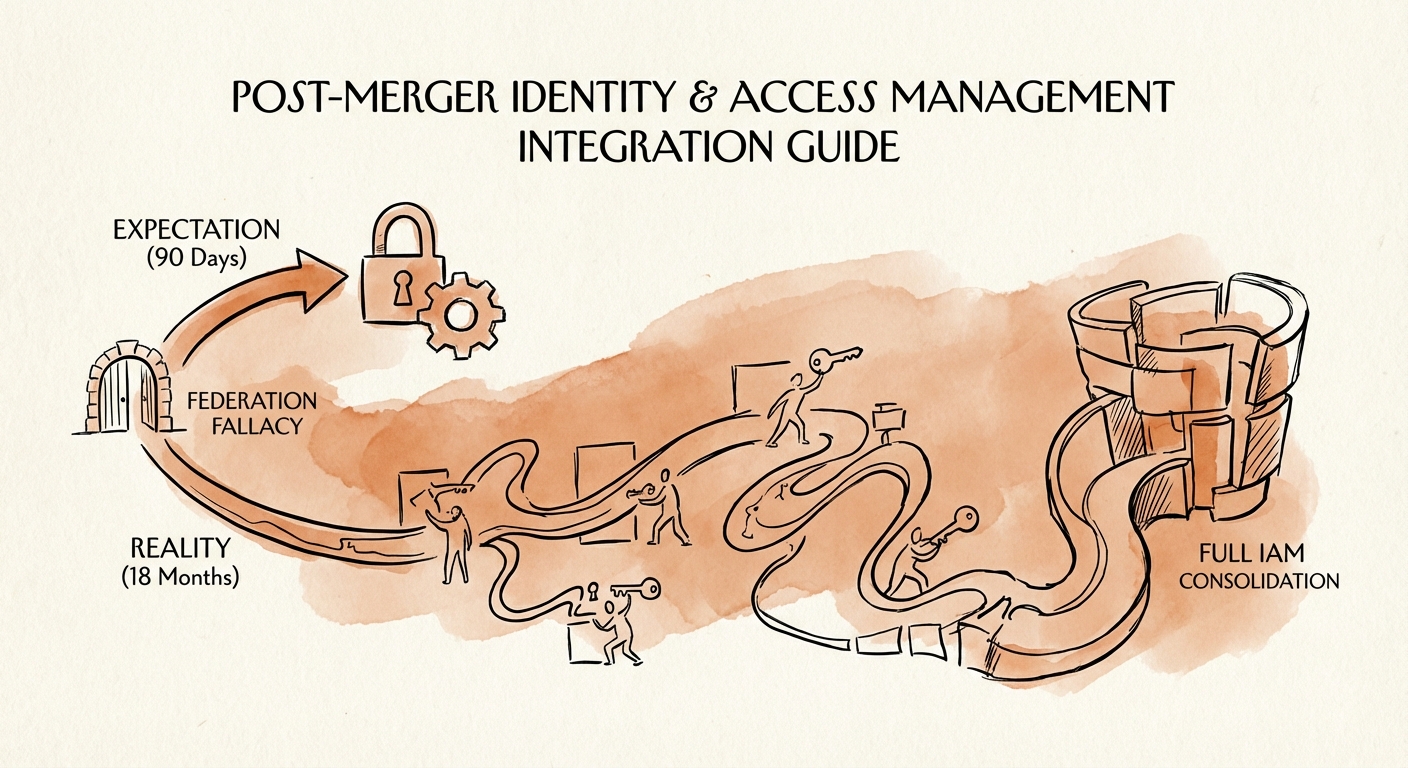
The 'Federation Fallacy' and the 18-Month Reality
A common dangerous assumption in the boardroom is that IAM integration is a 90-day project. In reality, while federation (allowing users to log in) takes days, true consolidation (retiring legacy directories) is a marathon. Benchmarks show that 63% of organizations underestimate the time required for IAM integration, with the average enterprise deployment stretching to 18-24 months. The gap between the 90-day expectation and the 18-month reality is where security debt accumulates.
The Hierarchy of Integration Risks
Effective IAM integration requires a triage approach, not a blanket "lift and shift." Transition leaders must categorize the acquired identity landscape into three risk tiers:
- Tier 1: Privileged Access (The Kill Zone). This includes Domain Admins, Global Admins, and root access to cloud environments. These identities must be inventoried and secured within the first 48 hours. The most common oversight here is "Shadow Admins"—users who aren't in the "Domain Admins" group but have ACL permissions that allow them to reset admin passwords.
- Tier 2: Service Accounts (The Silent Killer). Non-human identities often outnumber human users 5:1. In acquired technical debt, these accounts often run with excessive privileges and non-expiring passwords. Integrating these without breaking legacy applications is the primary driver of the 18-month timeline.
- Tier 3: User Identities (The Productivity Layer). This is where most integration teams start, but it is actually the lowest immediate risk if MFA is enforced.
The "Federation Fallacy" occurs when teams confuse Tier 3 success (users can email each other) with Tier 1 security. To avoid this, you need a Post-Acquisition Day 1 IT Checklist that explicitly separates connectivity from trust.
The 30-60-90 Day Consolidation Roadmap
To close the Ghost Access gap, abandon the "rip and replace" fantasy and adopt a structured containment strategy. This roadmap prioritizes risk reduction over administrative uniformity.
Day 0-30: Visibility and Containment
Do not create a two-way trust immediately. Instead, deploy a modern IdP (like Okta or Entra ID) to act as a "meta-directory." Ingest identities from both the parent and target directories into this centralized layer. This gives you a single pane of glass to see who has access to what, without merging the dirty underlying directories. Enforce a unified Multi-Factor Authentication (MFA) policy at this layer immediately. If the target company has legacy VPNs without MFA (a la Colonial Pipeline), shut them down and route access through the parent’s secure edge.
Day 31-60: The 'Shadow Admin' Hunt
Conduct a rigorous Cybersecurity Due Diligence deep dive on the acquired Active Directory. Use tools like BloodHound or PingCastle to map attack paths. You are looking for "toxic combinations" of entitlements that grant effective admin rights. Remove these privileges or delete the accounts entirely. This is also the phase to identify and freeze all "orphaned" accounts—identities that show no login activity for 90+ days.
Day 61-90+: Application Migration and Directory Decommissioning
Begin migrating applications from the target’s legacy authentication (LDAP/Kerberos) to modern standards (SAML/OIDC) pointed at your central IdP. This is the heavy lifting. Only once applications are unhooked from the legacy AD can you safely decommission the old domain controllers. This process will likely extend beyond Day 90, but by isolating the identity layer first, you have neutralized the lateral movement risk. For a deeper dive on technical debt in security, review our Technical Debt in Security Due Diligence Guide.