The $350M Invisible Liability
In the high-stakes world of M&A, security is often relegated to a compliance checkbox—a binary "pass/fail" based on SOC 2 reports or ISO certifications. This is a fundamental valuation error. True security technical debt is not about compliance; it is about deferred Capital Expenditure (CapEx). When you acquire a target with deep-seated security debt, you are not just buying risk; you are inheriting a remediation bill that will consume your engineering capacity for the first 12 to 18 months of the hold period.
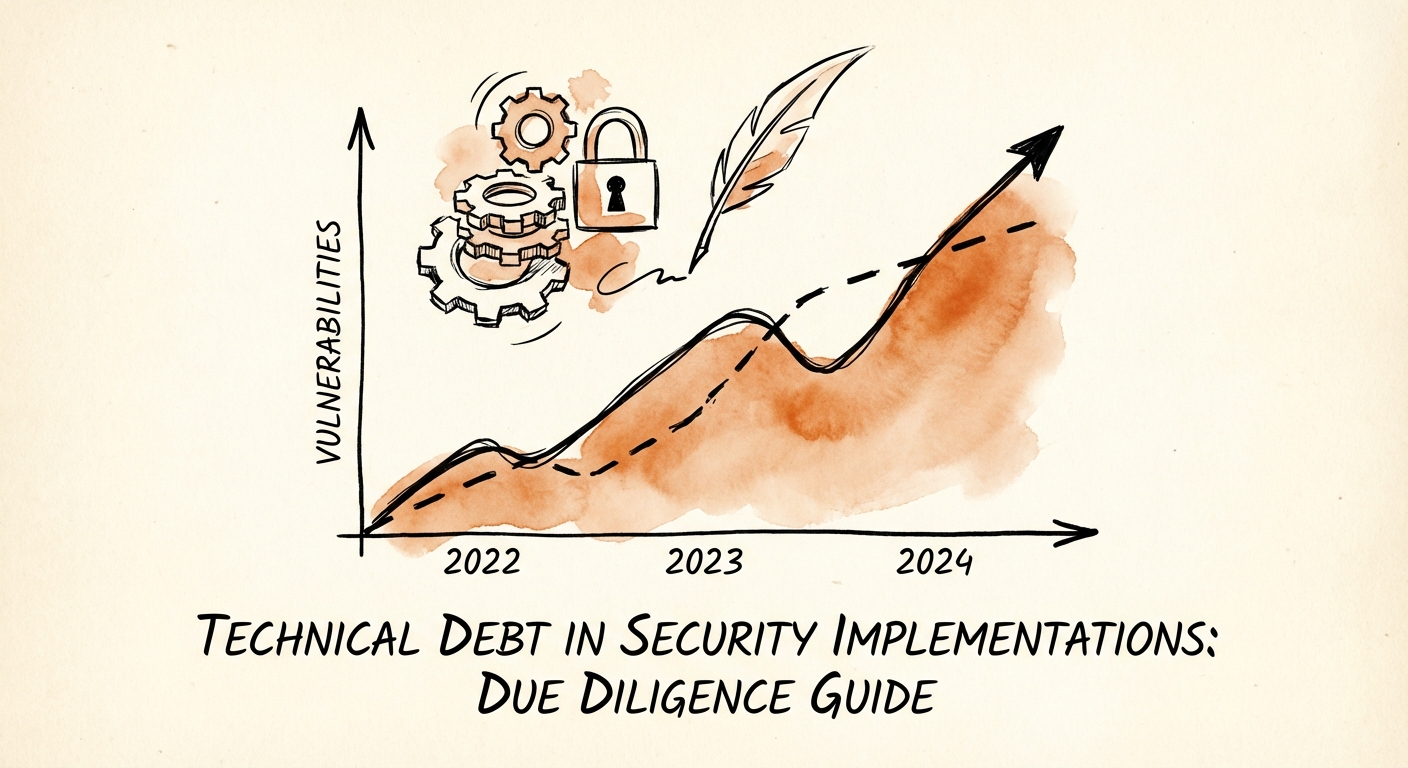
The market has already provided the ultimate cautionary tale: the $350 million valuation haircut in the Verizon-Yahoo deal. But while that was a headline-grabbing data breach, the silent killer in most mid-market deals is the remediation backlog. According to Synopsys' 2024 Open Source Security and Risk Analysis (OSSRA) report, 74% of commercial codebases now contain high-risk open source vulnerabilities, a massive jump from 48% the previous year. This means three out of every four potential acquisitions are running on compromised foundations before you even sign the LOI.
For Private Equity sponsors, this statistic transforms security from a generic "risk factor" into a quantifiable valuation lever. If 33% of the target's engineering team will be occupied fixing critical vulnerabilities instead of building the roadmap you underwrote in your investment thesis, your value creation plan is effectively dead on arrival. You are paying 100% of the price for 67% of the engineering velocity.
The 5-Day Diagnostic Framework
Traditional IT due diligence checklists are insufficient for quantifying this specific type of debt. They ask, "Do you have a firewall?" rather than "How many hardcoded secrets are in your repositories?" To accurately assess security debt, you must shift from questionnaire-based diligence to evidence-based auditing. We recommend a rapid, 5-day diagnostic focused on three high-signal areas.
1. The Codebase Toxicity Audit
Do not rely on the target's self-reported scan results. Request a raw export of their Software Composition Analysis (SCA) logs or run a blinded scan. You are looking for high-severity vulnerabilities older than 90 days. Veracode's 2024 research indicates that 46% of organizations carry persistent, high-severity flaws that have been ignored for over a year. This is not "backlog"; this is negligence that you will pay to fix.
2. The Identity Sprawl Check
In modern SaaS architectures, identity is the new perimeter. Ask for a report on over-privileged service accounts and hardcoded credentials. A specialized scan often reveals that 20-30% of "secure" applications have API keys or database credentials committed directly to the code. Remediation here involves not just deleting the keys, but re-architecting the entire secrets management workflow—a project that can take months.
3. The 'Lift and Shift' Cloud Tax
Many targets claim to be "cloud-native" but are actually "cloud-hosted." Look for flat network topologies in AWS or Azure where development and production environments share VPCs. This infrastructure technical debt requires a complete re-platforming to meet enterprise security standards, a cost that rarely appears in the Quality of Earnings (QofE) report.
Quantifying the Remediation Cost
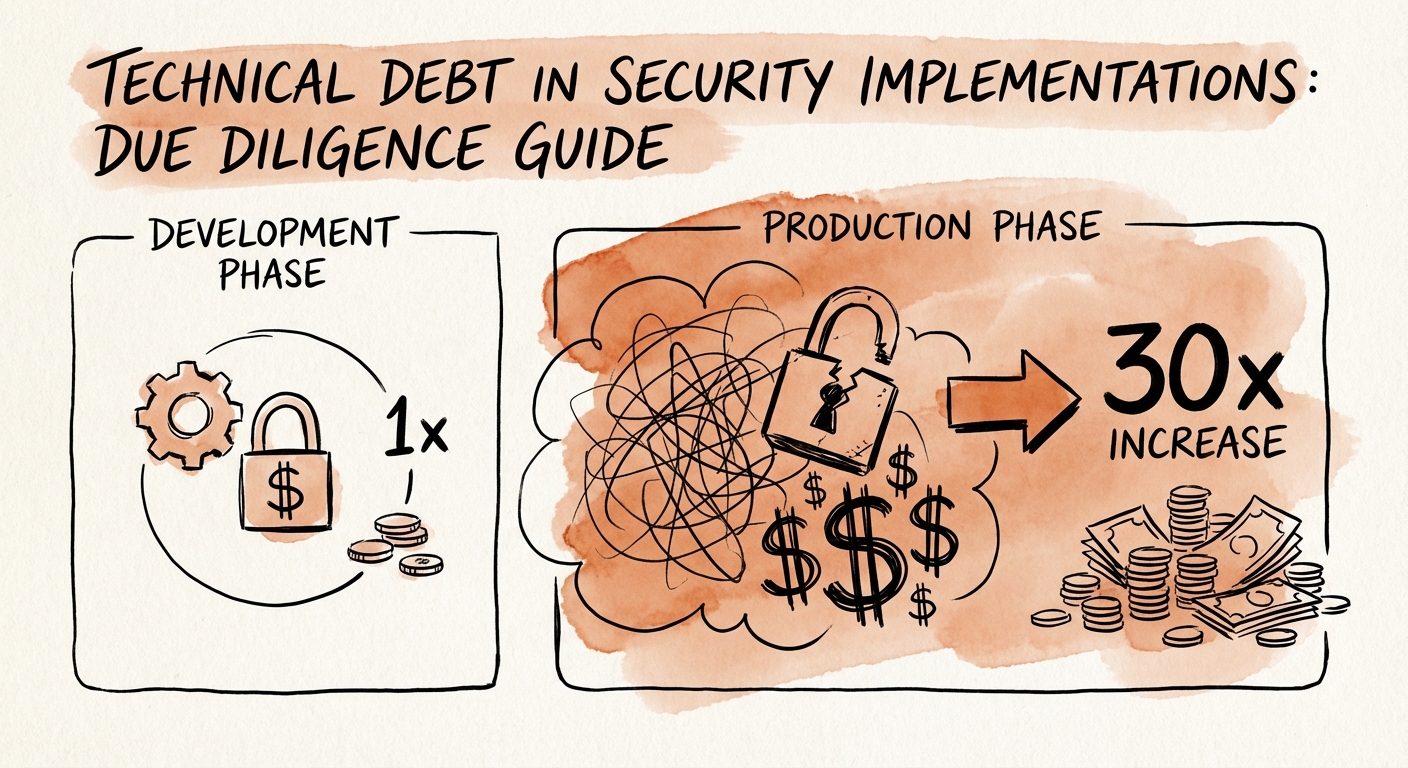
Once you have identified the debt, you must price it. The most common mistake PE firms make is underestimating the remediation multiple. Fixing a vulnerability in production is not a linear cost; it is exponential. Industry benchmarks consistently show that remediating a defect in production costs roughly 30x more than fixing it during the design phase.
Furthermore, the time-to-remediate is the metric that kills deal momentum. The average time to fix a critical vulnerability is currently 205 days. If your target has 50 critical vulnerabilities, you are not looking at a weekend patch party; you are looking at a structural drag on EBITDA that will persist for the first two quarters of ownership.
The Purchase Price Adjustment (PPA)
Use these findings to negotiate. If your diagnostic reveals $2M in necessary security remediation engineering hours, this should be treated as a working capital adjustment or a specific indemnity, not just an operational headache. Smart sponsors are now inserting "Technical Debt Covenants" into closing documents, requiring specific remediation milestones post-close, funded by a holdback escrow. This aligns the seller's incentives with the reality of the asset they are handing over.