The 'Black Box' Valuation Trap: Why Algo Efficacy Matters More Than Code Quality
In traditional software due diligence, we look for clean code, scalable architecture, and documentation. In cybersecurity M&A, those are table stakes. The real valuation driver—and the biggest risk factor—is efficacy. You aren't just buying code; you are buying a detection capability.
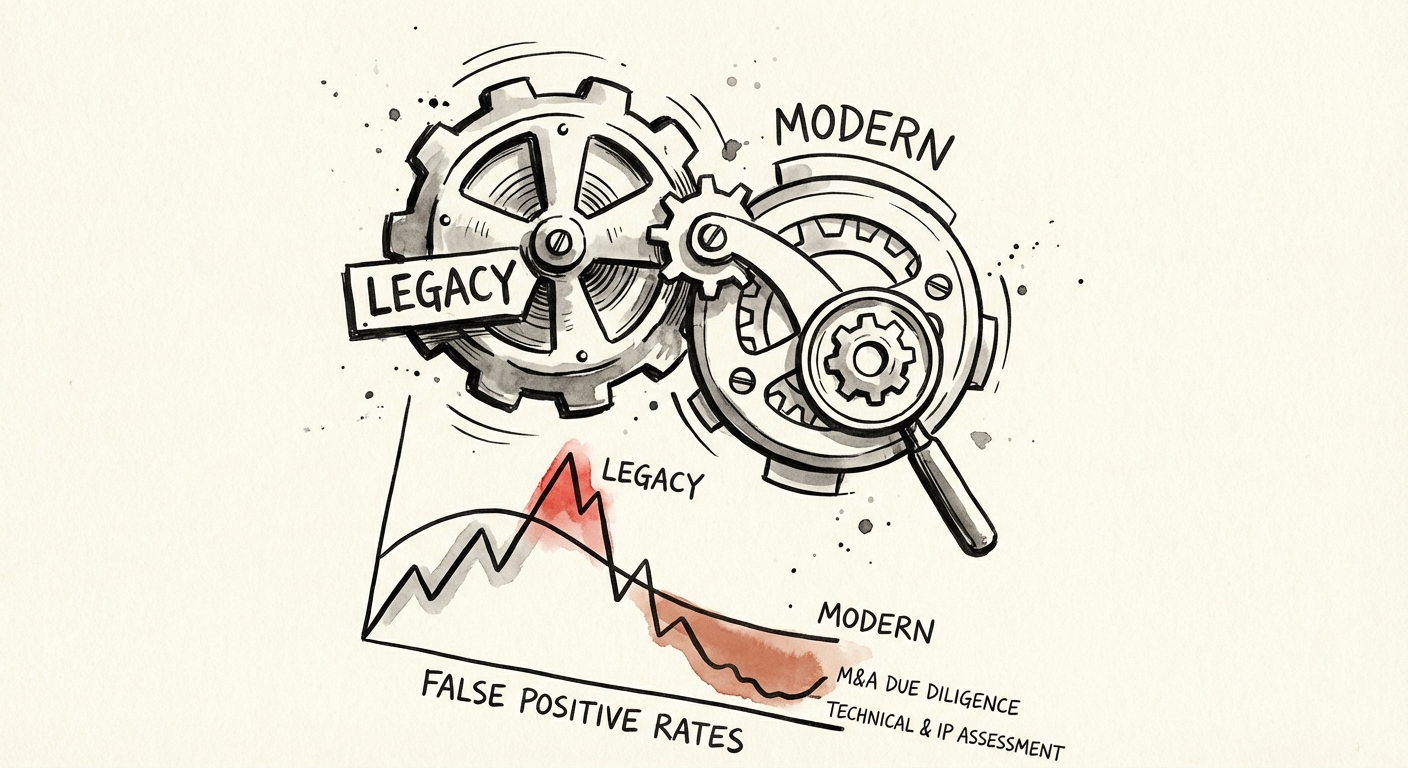
Most Private Equity sponsors get burned because they treat a cybersecurity acquisition like a standard SaaS deal. They see "AI-powered threat detection" in the CIM and assume it works. Here is the reality I see in the trenches: heavily marketed "AI" solutions often operate with false positive rates as high as 53%. That is not a product feature; that is a margin-killing operational tax. If the tool generates more noise than signal, your post-acquisition roadmap won't be about scaling sales—it will be about hiring an army of support engineers to triage alerts for angry customers.
When we diligence a target, we don't just read the code; we replay traffic. We benchmark the False Positive Rate (FPR). Best-in-class endpoint security achieves an FPR of roughly 0.13%. If your target is sitting at 5% or 10%, you are not buying a software company; you are buying a low-margin services business disguised as a tech platform. That delta destroys your Rule of 40 metrics and erodes the 80%+ gross margins you modeled.
The Open Source Liability: When 'Proprietary' IP Is Actually GPL-Infected
The single fastest way to kill a deal's value is IP contamination. In 2025, 99% of audited M&A transactions involved open source components, with an average of 2,778 distinct components per codebase. That usage itself isn't the problem; the licensing governance is.
I recently audited a Series C security firm asking for a 12x multiple. They claimed a proprietary "behavioral analysis engine." My team found that their core detection logic was a hard-linked wrapper around a GPL-licensed library. This "infection" meant that, legally, their entire proprietary codebase could be forced into the public domain. The deal didn't just re-trade; it collapsed.
For a PE Operating Partner, this is a binary risk. You cannot fix a GPL violation post-close without a complete rewrite, which freezes your roadmap for 12-18 months. During due diligence, you must demand a Software Bill of Materials (SBOM) and run an automated composition analysis. If you find high-risk "copyleft" licenses in the core IP, you are looking at a 100% valuation write-down of that asset. Do not accept "we'll patch it later" as an answer. The legal exposure exists the moment you sign.
Technical Debt in Security: The Agent Bloat Factor
In cybersecurity, technical debt doesn't just slow down developers; it prevents deployment. The "agent vs. agentless" debate is critical here. If you are acquiring an endpoint detection and response (EDR) player, the weight of their agent is a direct correlation to churn risk.
We measure Deployment Friction in days. A modern, low-debt security product should deploy to 10,000 endpoints in under 48 hours. I've seen legacy targets with massive "agent bloat"—spaghetti code on the client side—where deployment takes 4 to 6 weeks of professional services hand-holding. That friction kills your Land-and-Expand strategy.
Furthermore, 33% of developer time in these debt-ridden firms is wasted on maintaining brittle legacy agents rather than building new detection capabilities. When you model your synergy capture, you must account for this. You will likely need to burn 6 months of EBITDA just to refactor the agent to a deployable state. If you don't factor this "remediation tax" into your working capital adjustment, you are overpaying.