The Valuation Gap: Why You Are Hunting in the AppExchange
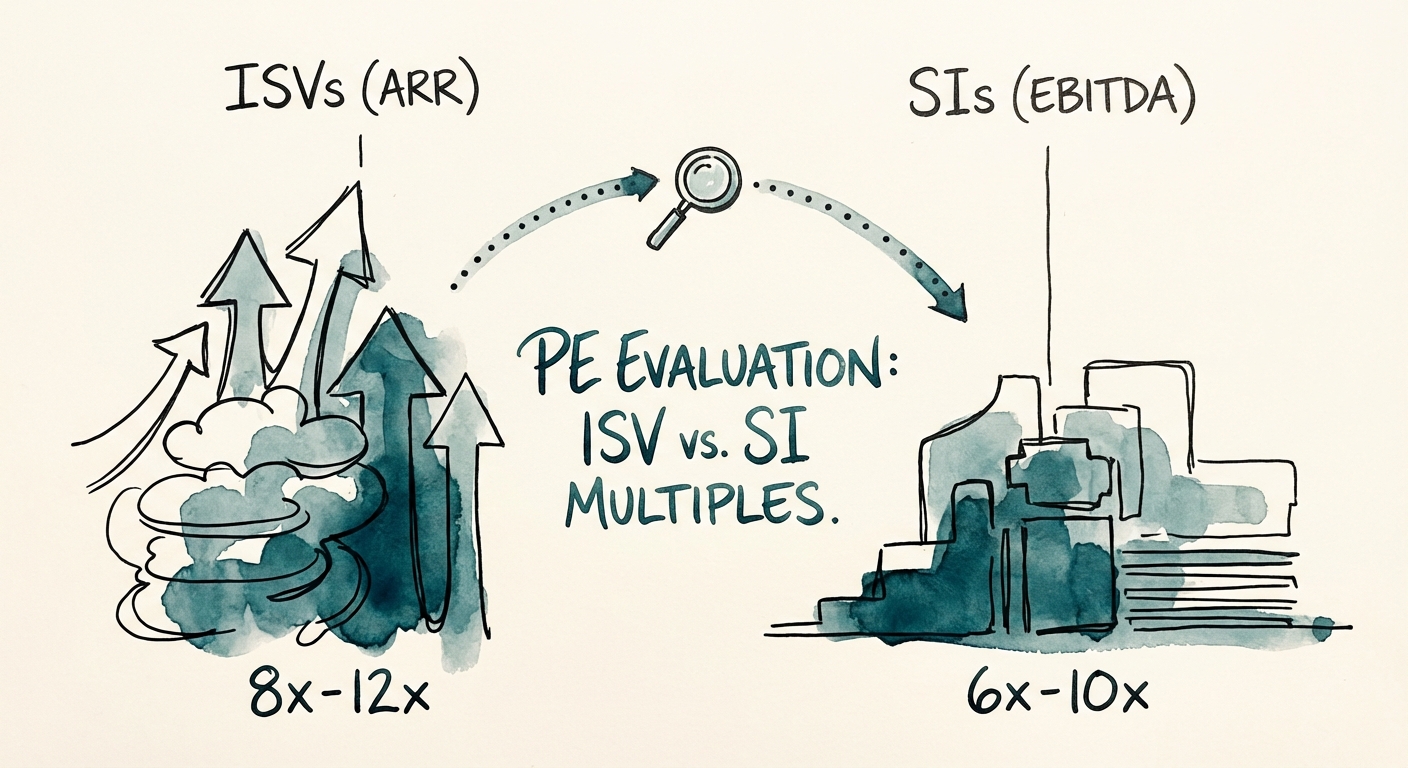
As a PE Operating Partner, you know the math better than anyone. A Salesforce System Integrator (SI) trades at 6x-10x EBITDA. A true Salesforce ISV (Independent Software Vendor) trades at 6x-12x ARR. The arbitrage play is obvious: acquire a vertical-specific ISV, professionalize its sales motion, and exit at a software multiple.
But in 2026, the lines have blurred. We are seeing a proliferation of "Fake ISVs"—companies pitching themselves as SaaS products when they are actually tech-enabled services firms with a managed package wrapper. They claim 85% gross margins, but a look at their P&L reveals that 30% of their "subscription" revenue is actually recurring professional services (managed services) disguised as ARR.
If you pay an ARR multiple for a services business, your fund’s returns are dead on arrival. The market is currently punishing this ambiguity. While premium vertical SaaS ISVs are trading near 7.8x Revenue, those with murky revenue mixes are being re-rated down to 2x-4x Revenue during Quality of Earnings (QofE). You cannot afford to discover this distinction after the deal closes.
The Technical Diligence Minefield: Security Review as a Deal Killer
Financial engineering can't fix a broken codebase. The single biggest deal-killer in Salesforce ISV acquisitions isn't churn—it's Technical Debt, specifically regarding the Salesforce Security Review.
Salesforce estimates that 50% of applications fail their first Security Review. For a portfolio company, a failed review isn't just a badge of shame; it is a commercial freeze. If your target gets delisted or blocked from updating their package due to security violations (SOQL injection, Cross-Site Scripting, or CRUD/FLS enforcement failures), their sales cycle stops cold. You cannot sell what you cannot install.
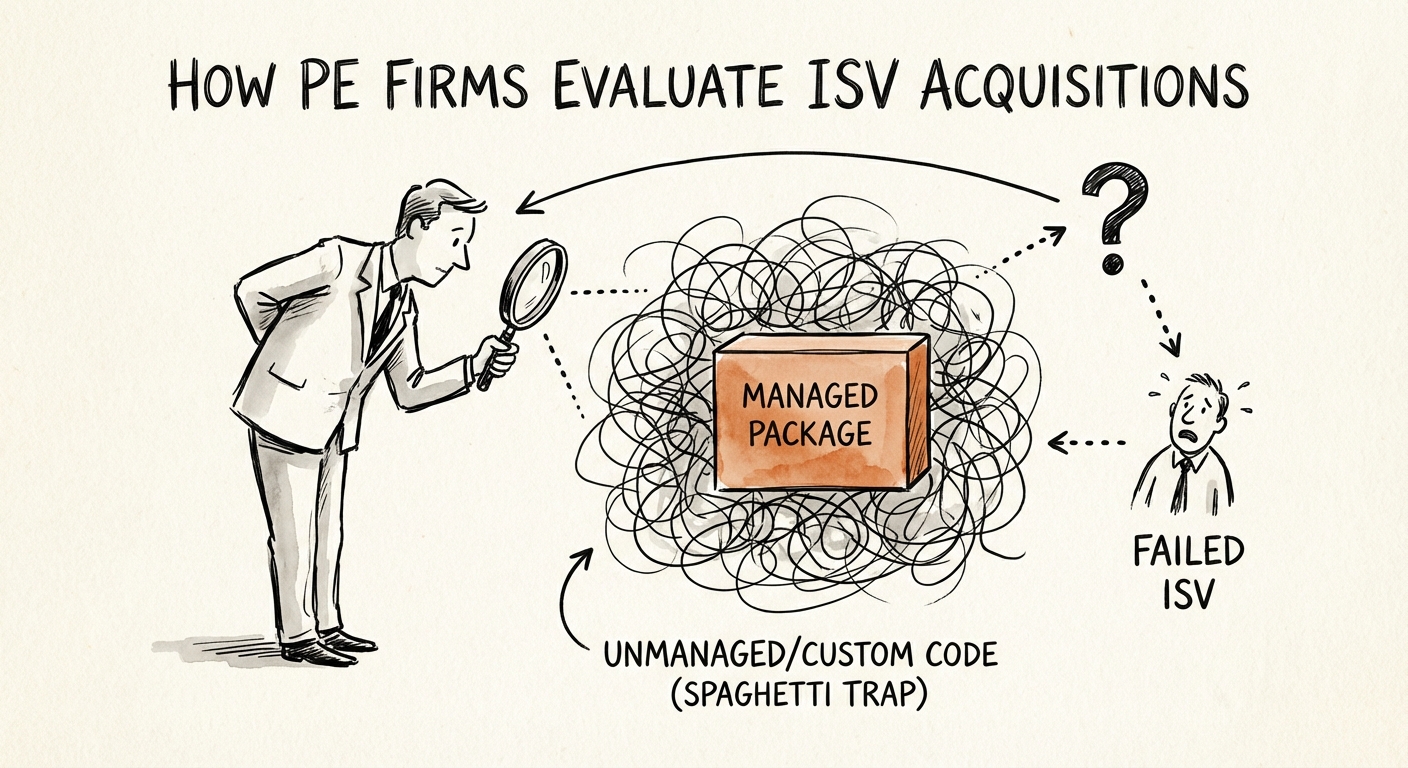
The "Spaghetti Code" Trap
We recently audited a target claiming to be a "healthcare compliance ISV." The diligence revealed that while they had a managed package, 60% of their logic lived in unmanaged customized Apex triggers deployed directly into customer orgs. They weren't maintaining a product; they were maintaining 50 separate forks of a codebase. The cost to remediate this technical debt was estimated at $2.4M and 18 months—effectively wiping out the projected synergy for the first two years of the hold period.
True ISVs have 90%+ code coverage (well above the 75% minimum) and automated CI/CD pipelines. If your target relies on "Change Sets" for deployment, you are buying a services firm, not a software company.
The Remediation Playbook: Fix It or Re-Trade It
If you identify these technical red flags pre-close, you have leverage. You don't necessarily have to walk away, but you must structure the deal to account for the remediation cost.
1. The Security Retainer
Require a Security Remediation Escrow. If the target has not passed a Security Review in the last 12 months, hold back 10-15% of the purchase price until they do. This aligns the founder's incentives with technical reality.
2. The Revenue Re-Classification
Force a strict separation of License Revenue vs. Services Revenue in the QofE. Any revenue attached to "implementation success" or "ongoing configuration" moves to the Services bucket. Valuate that portion at 1x Revenue (or 6x EBITDA), not the 8x ARR multiple the banker is asking for.
3. The Code Consolidation Roadmap
Demand a 100-day plan specifically for Package Unification. If they have bespoke code across clients, the first priority of your new CTO must be migrating core features into the base managed package. Without this, you cannot scale efficiently, and your exit multiple will collapse when the next buyer does their diligence.
For a deeper dive on how we assess these risks, review our guide on The Hidden Costs of Salesforce Customization or compare the valuation dynamics in Salesforce Implementation Partner Valuations.