The 'Trust Deficit' is a Valuation Lever
In 2026, a target company's security posture is no longer just an IT concern—it is a direct proxy for revenue quality. For Private Equity sponsors, the absence of a SOC 2 Type II report isn't merely a checklist failure; it is a 12-month revenue freeze on enterprise deals. If your investment thesis relies on moving a mid-market SaaS player upmarket to the Global 2000, a missing or deficient SOC 2 report effectively pauses that strategy for the duration of the observation period (minimum 6 months) plus remediation time (3-6 months).
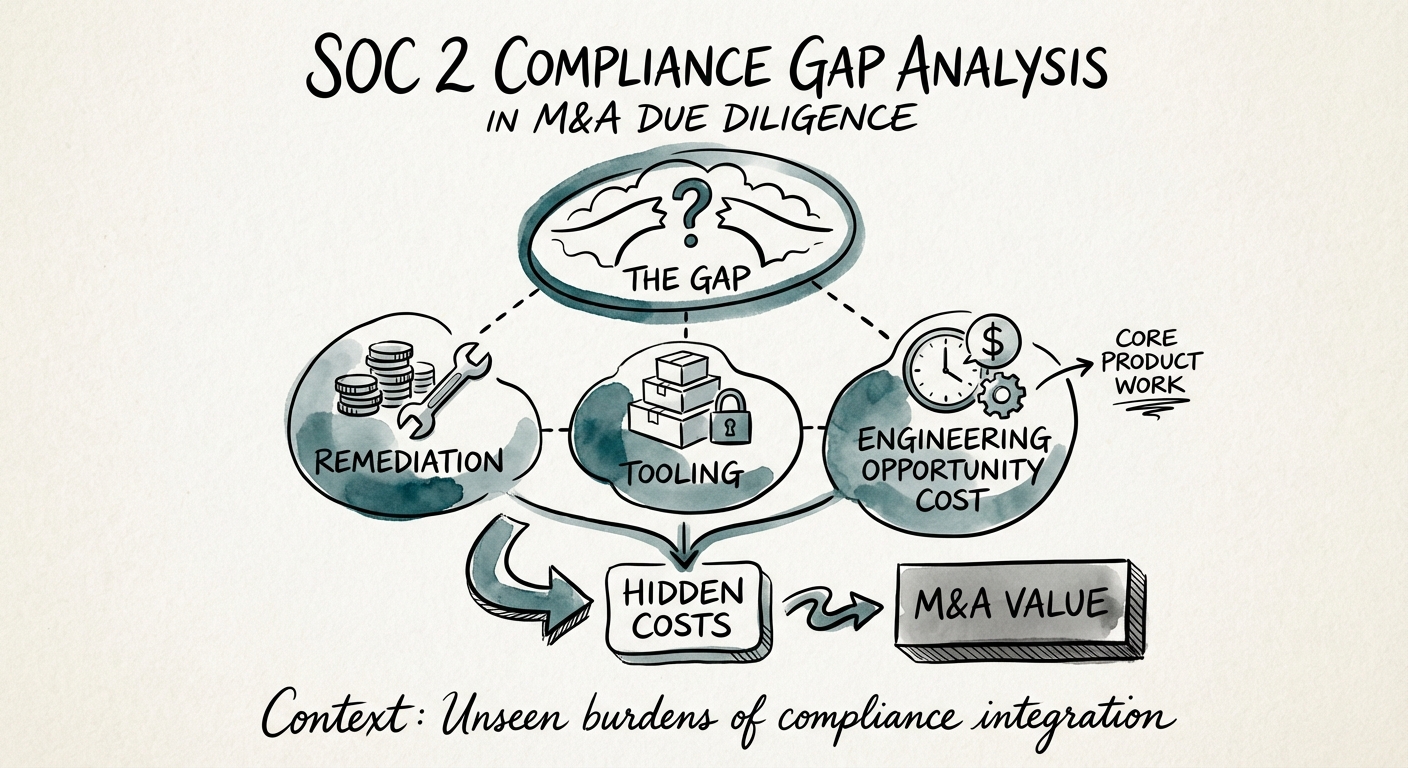
The Hidden Cost of 'Compliance Debt'
While a standard SOC 2 Type II audit might cost $75,000 to $150,000 in direct fees, the total cost of ownership (TCO) to achieve first-time compliance is often 2x to 3x that figure when factoring in remediation, tooling, and engineering opportunity cost. Our data indicates that a mid-market SaaS firm with no prior compliance history carries a hidden liability of approximately $350,000. This figure represents the capital injection required to build a security program capable of passing an audit, not just paying for the certificate.
Furthermore, this debt compounds. Without a SOC 2 report, your target is likely signing 'security addendums' in customer contracts that expose them to uncapped liability or onerous breach notification terms. In due diligence, you must quantify this price of compliance gaps as a direct reduction in Enterprise Value, ensuring you have the dry powder post-close to fund the remediation.
The 'Paper Tiger' Diagnostic: Spotting Fake Compliance
Sophisticated sellers will often present a 'security package' that looks robust on the surface but collapses under scrutiny. We call these 'Paper Tiger' programs—they look fierce but have no teeth. During the exclusivity window, Operating Partners must look beyond the existence of a certificate and audit the scope and quality of the attestation.
Red Flags in the Data Room
Your technical due diligence team should aggressively hunt for these three indicators of a hollow security program:
- Type I vs. Type II: A SOC 2 Type I report only tests the design of controls at a single point in time. It proves nothing about operational effectiveness. If a target only has a Type I, they are not 'compliant'—they are merely 'prepared.'
- The 'Carve-Out' Trick: Check the system description section of the report. Did they exclude their cloud hosting provider? Did they carve out the specific product line driving your revenue growth? A report that only covers the corporate IT environment but excludes the SaaS platform is worthless for enterprise sales.
- Qualified Opinions: A 'Qualified Opinion' means the auditor found material failures. While rare in final reports (companies usually delay issuance to fix them), finding a history of qualified opinions or 'management responses' indicating exceptions in prior years suggests a systemic cultural failure to maintain security, not just a technical gap.
Identifying these gaps early allows you to structure a 90-day acceleration playbook post-close, rather than being blindsided by a failed audit in Year 1.
From Liability to Leverage: The Retrade Framework
Once you have quantified the Compliance Debt, use it. Smart sponsors are increasingly using the 'Cost to Cure' as a specific line item in the Quality of Earnings (QofE) or as a working capital adjustment. If the target claims to be 'Enterprise Ready' but lacks a SOC 2 Type II, they are misrepresenting their market readiness.
Calculating the Remediation Budget
Don't rely on the target's estimate. They will quote you the audit fee ($40k-$60k). You must budget for the reality:
- vCISO / GRC Leadership: $15k/month for 6 months.
- Compliance Automation Tooling: $20k-$30k annually (e.g., Drata, Vanta, Secureframe).
- Penetration Testing: $15k-$25k per year.
- Engineering Remediation: 20% of engineering capacity for one quarter to fix access controls, encryption, and logging gaps.
By presenting this detailed 'Cost to Cure' analysis, you justify a valuation adjustment that covers your Year 1 security roadmap. More importantly, you prevent the $350M horror stories where security debt explodes into a breach shortly after acquisition.