The Trojan Horse in Your Deal
You are buying a cybersecurity company to protect your portfolio's digital assets, or perhaps to add a "crown jewel" to your platform. The thesis is simple: they have proprietary IP that creates a defensive moat. But in 2025, that moat is often built on quicksand.
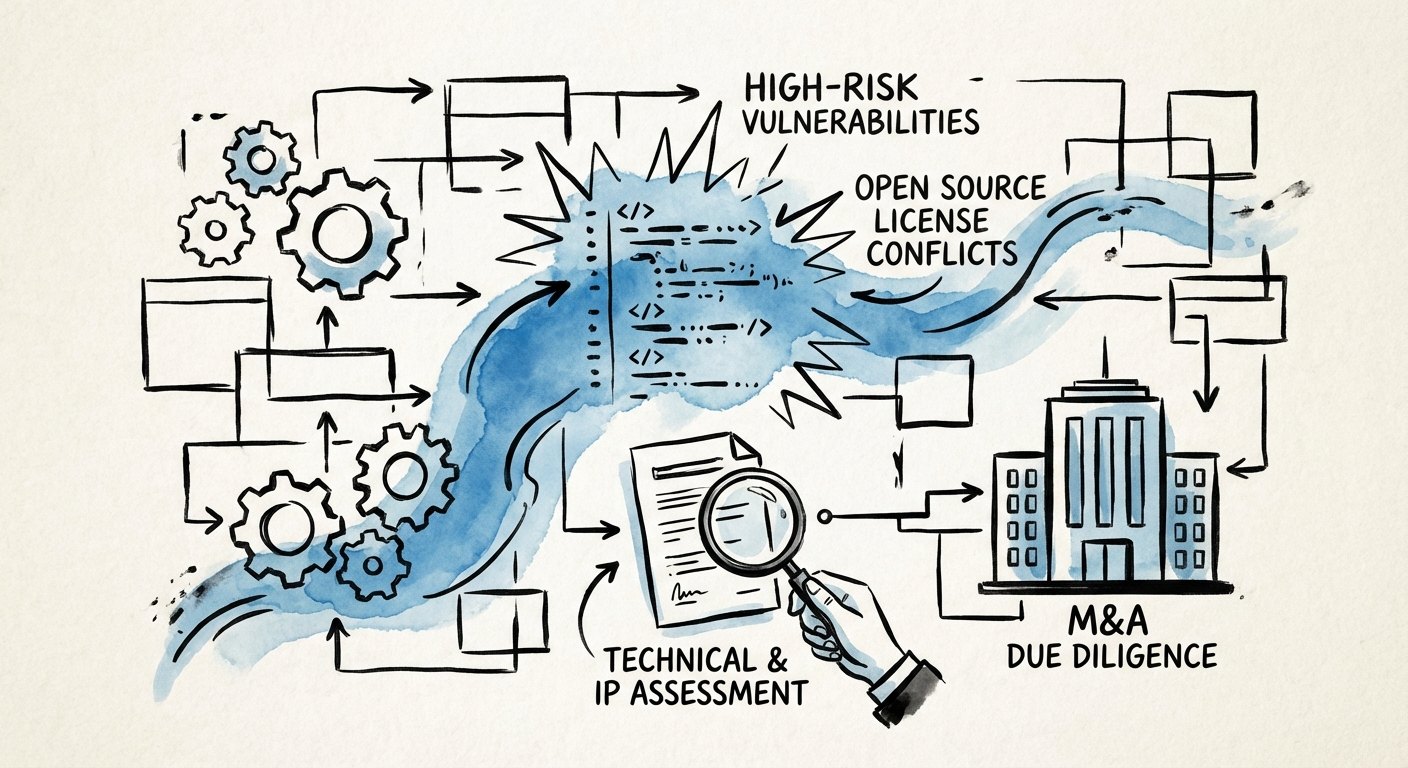
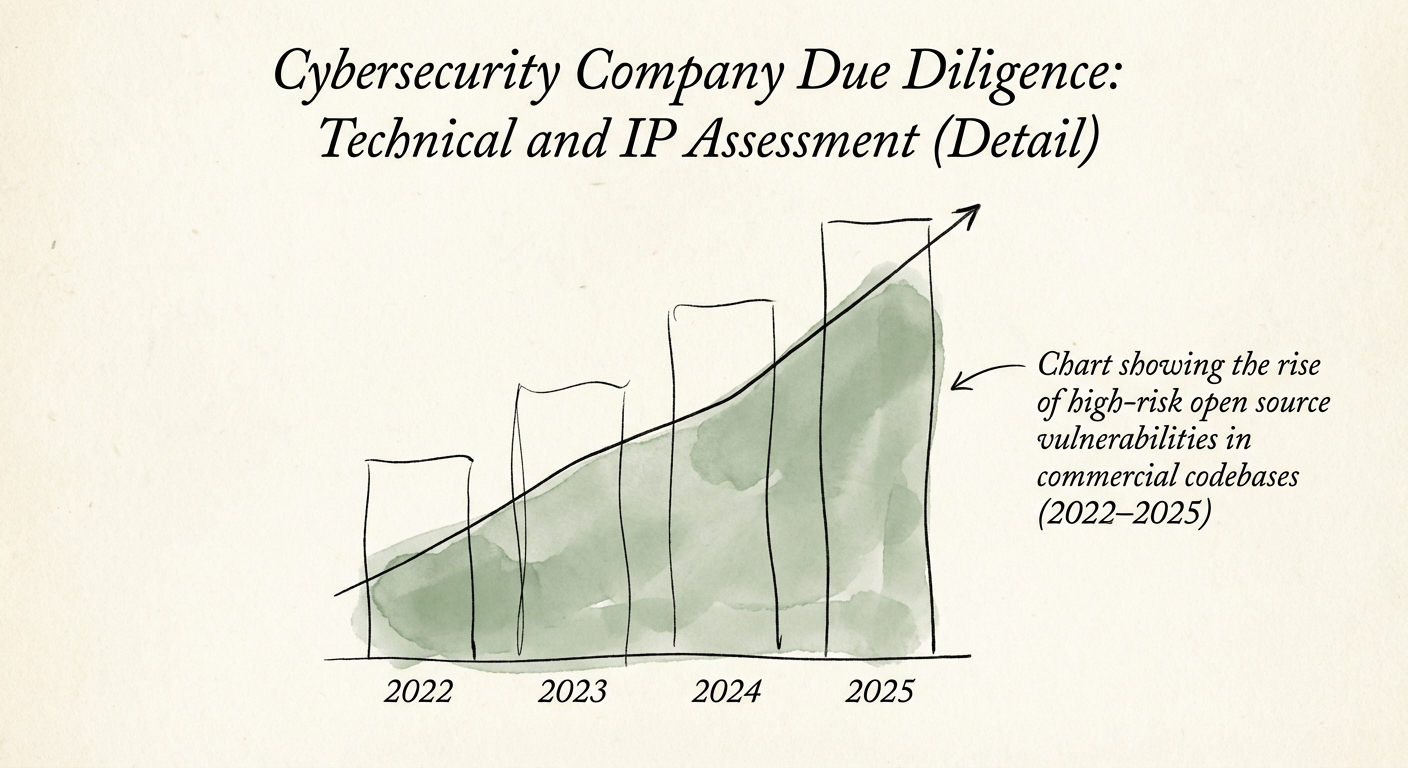
Here is the reality of the modern software supply chain: 96% of commercial codebases contain open source components. That isn't a problem in itself; it's how modern software is built. The problem is that 74% of those codebases contain high-risk vulnerabilities, according to the latest Synopsys data. When you acquire a cybersecurity firm, you aren't just buying their revenue and their roadmap; you are inheriting their technical debt and their unpatched vulnerabilities.
For a Private Equity Operating Partner, this presents a paradox. You are paying a premium for "security expertise," yet the target's own house may be built with combustible materials. If you fail to assess the underlying code quality and IP ownership before close, you risk acquiring a liability that will stall your roadmap for 18 months while your expensive engineering team rewrites the "proprietary" platform you just bought.
The 3-Point Diagnostic: What to Look For
When conducting technical due diligence on a security asset, financial audits and high-level architecture reviews are insufficient. You need to look at the code, the contributors, and the licenses. Here is the diagnostic framework.
1. The Open Source Minefield
Your target claims their algorithm is proprietary. In reality, 76% of the code is likely open source. The risk isn't just security; it's legal. If they have used components with "copyleft" licenses (like GPL) in their distributed software, they may be legally required to open-source their entire proprietary codebase. Synopsys reports that 53% of codebases contain license conflicts. During DD, you must demand a Software Bill of Materials (SBOM) and run a composition analysis scan (SCA).
2. The "Contractor Trap" in IP Ownership
Did the developer who wrote the core encryption engine actually assign the IP to the company? In early-stage security startups, founders often pay offshore contractors to build the MVP. If the Intellectual Property Assignment agreements weren't signed—or if they were signed after the code was written without a "prior inventions" clause—the company doesn't own its product. I have seen deals stall because a freelancer in Eastern Europe technically owned the platform's core library.
3. Technical Debt as a Valuation Killer
Technical debt isn't just an engineering complaint; it's a cap on your future EBITDA. Data shows that 33% of developer time is wasted on technical debt rather than innovation. If the target's engineering team is spending a third of their time fixing spaghetti code, your value creation plan is effectively 33% slower than you modeled. You need to quantify this debt in dollars, not abstract "code quality" scores.
For a deeper dive on quantifying this risk, read our guide on Technical Debt is Financial Debt: The M&A Due Diligence Playbook.
The Action Plan: 10 Days to Certainty
Don't rely on the CIM or the CTO's PowerPoint. Request these specific items in the Data Room immediately.
- Automated Composition Analysis (SCA) Report: Do not accept a manual spreadsheet. Demand a scan from Black Duck, Snyk, or similar tools. If they refuse, it's a red flag.
- Git Repository Contribution History: Map the top 5 contributors. Are they current employees? If they are contractors, pull their IP assignment agreements immediately.
- The "Grand Rewrite" Test: Ask the CTO, "If you could rewrite one part of the system, what would it be?" If the answer is "the core engine," price in a 12-month roadmap delay.
If you find significant technical debt or IP gaps, you don't necessarily have to kill the deal. Use it. We frequently see PE firms use quantified technical debt assessments to negotiate 10-15% discounts on the enterprise value, creating an immediate budget for remediation post-close.
For a complete checklist of what documents to request, reference The 'Dirty Dozen': 12 IT Due Diligence Documents That Reveal the Truth. And if you are worried about the broader security posture of the target, verify their claims against The Security Posture Assessment checklist.
Conclusion
In cybersecurity M&A, the code is the business. If the code is broken, or if the company doesn't own it, the business is worthless. Verify the technical foundation with the same rigor you apply to the Quality of Earnings.