The Compliance Mirage in MSP Consolidation
The MSP consolidation wave is creating a dangerous blind spot in private equity portfolios. As PE firms race to roll up regional providers into national platforms, they often rely on standard "check-the-box" due diligence: Is there a SOC 2 report? Is there cyber insurance? Do they have a policy handbook?
This is the Compliance Mirage. A SOC 2 Type II report tells you that controls were designed and operated over a lookback period; it does not tell you if the MSP’s RMM (Remote Monitoring and Management) tool—the "God Mode" software that controls thousands of client endpoints—is currently sitting open to the internet without MFA. It does not tell you if their "patch management" SLA is a marketing promise or an operational reality.
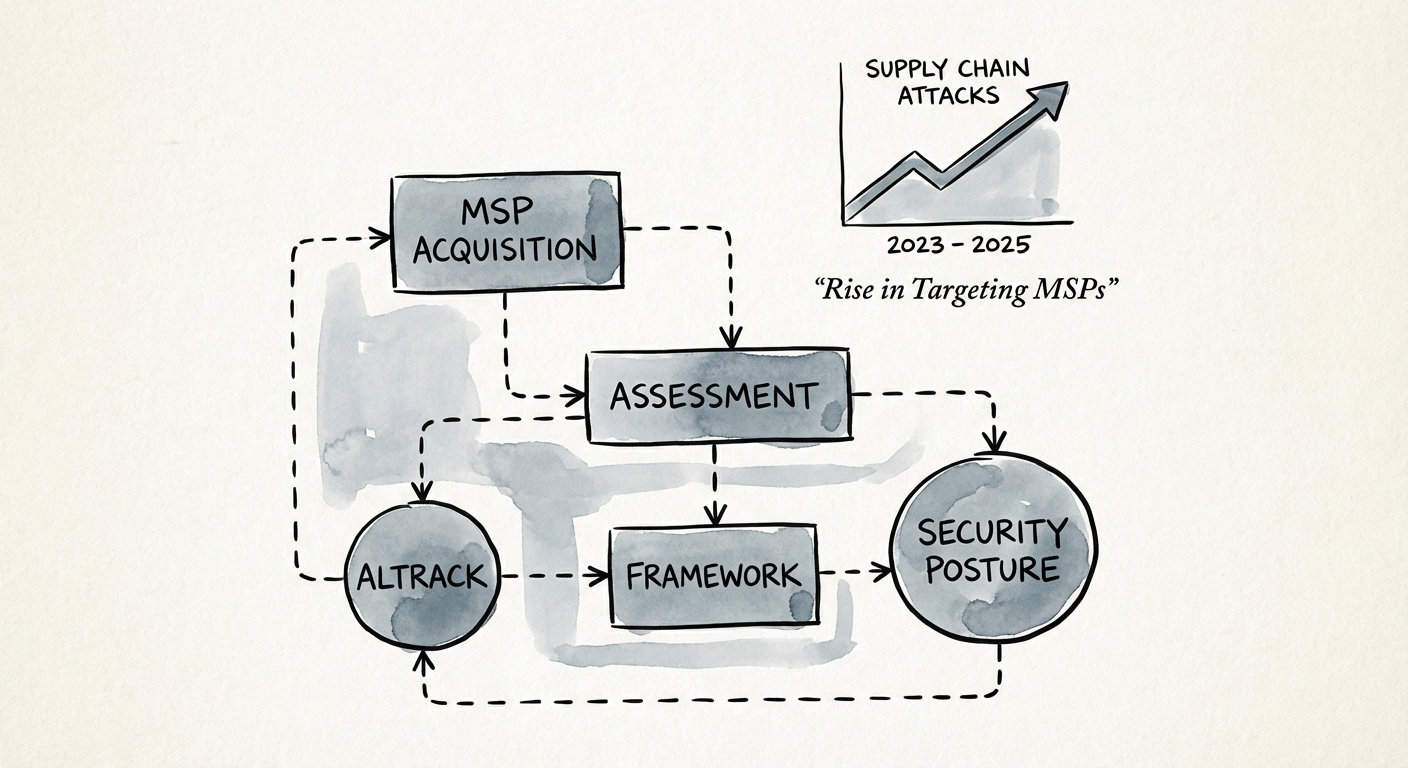
The stakes have shifted. According to Verizon’s 2025 Data Breach Investigations Report, breaches involving third parties—specifically supply chain attacks—have doubled to 30%. For an MSP, this is existential. An MSP is not just a target; it is a distribution channel for ransomware. A single compromise in an acquired MSP’s toolset doesn’t just infect one company; it infects the entire downstream client base, triggering a cascade of liability that can exceed the enterprise value of the platform itself.
In 2024, the average cost to recover from a ransomware attack reached $2.73 million, excluding the ransom itself. For a platform MSP strategy, the risk is multiplicative. You aren't just buying EBITDA; you are buying a potential contagion event. To protect deal value, acquirers must move beyond compliance artifacts and conduct an operational security posture assessment.
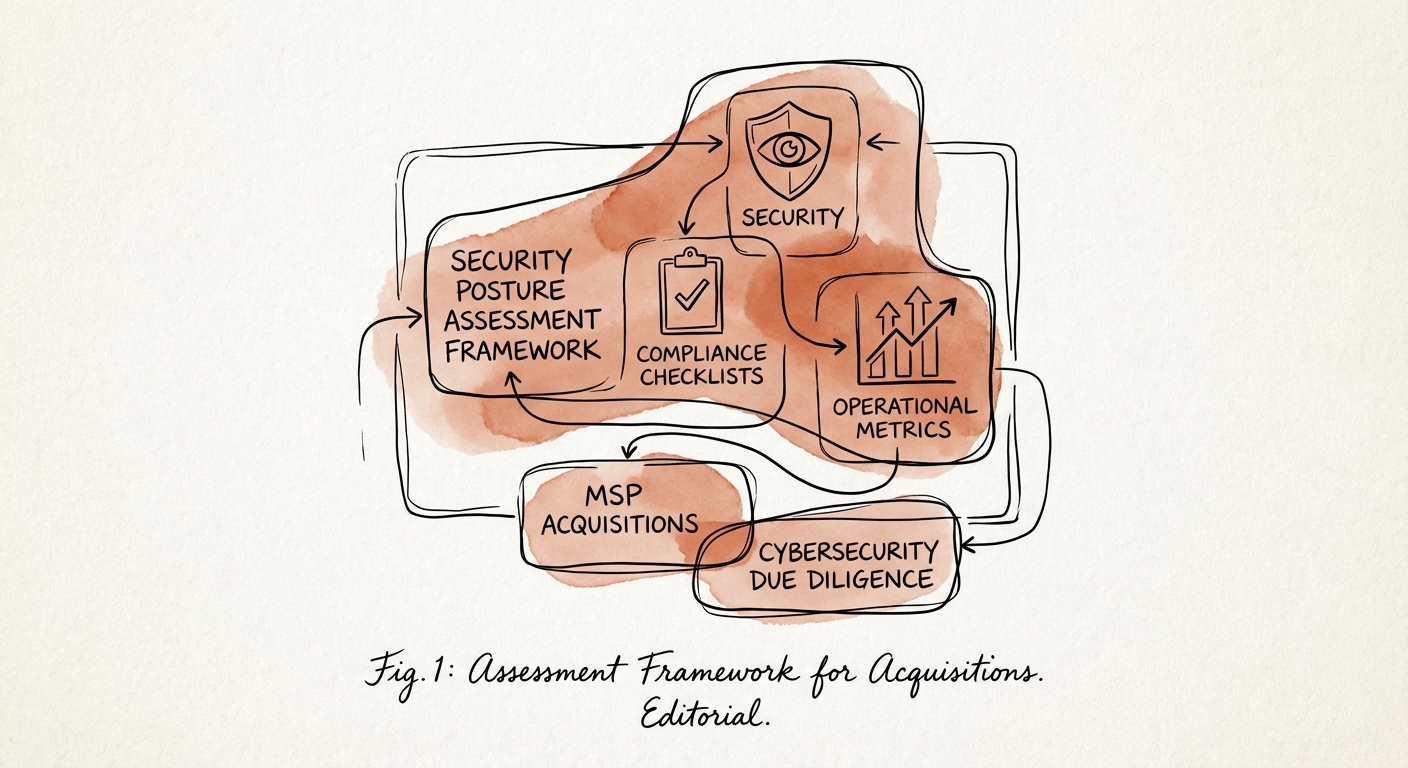
The 5-Point Operational Assessment Framework
Effective cybersecurity due diligence for MSPs requires looking under the hood of the "factory"—the tools and processes used to deliver services. Use this 5-point framework to assess operational reality vs. sales presentation.
1. The "God Mode" Audit (RMM & PSA Security)
The RMM tool is the crown jewel for attackers. If they breach this, they own every client. Assessment Check: Do not just ask if they have MFA. Ask for the specific configuration of the RMM instance. Is it accessible via the public internet? Is MFA enforced at the system level or the user level (where it can be bypassed)? Are there "break-glass" accounts with static passwords? A surprising number of MSPs still share "admin" credentials for emergency access. This is a deal-killer.
2. Identity Governance Efficacy
Most MSPs manage client identities (Azure AD/Entra ID) but fail to manage their own. Assessment Check: Audit the offboarding process. Pick 5 employees who left in the last 12 months. Were their accounts in the PSA (Professional Services Automation) tool, RMM, and documentation platform revoked within 24 hours? In our experience, 40% of MSPs have active accounts for former technicians, leaving a wide-open backdoor.
3. The "Patch Gap" Analysis
Every MSP claims to patch systems within 30 days. Assessment Check: Ignore the policy document. Request a raw export from their vulnerability scanner for a random sample of 10% of their managed endpoints. Compare the "first detected" date of critical vulnerabilities against the current date. If the delta averages 90+ days while the SLA says 30, you have found a hidden liability. This operational failure indicates deep technical debt in security implementations.
4. EDR/MDR Coverage Reality
Does the MSP deploy Endpoint Detection and Response (EDR) on 100% of endpoints, or only for clients who pay extra? Assessment Check: Security is a herd immunity problem. If the MSP allows "budget" clients to remain on legacy antivirus while sharing the same network or RMM infrastructure as "premium" clients, the risk is shared. A breach in a low-value client can propagate up to the MSP’s core infrastructure.
5. Resilience & The "Air Gap"
When ransomware hits, backups are the first target. Assessment Check: Are client backups immutable (read-only)? Can the MSP demonstrate a restore test from the last 90 days that wasn't just a screenshot of a success message? If the backup console is on the same domain as the RMM, there is no air gap. A single compromise wipes both the production data and the safety net.
Calculating Security Debt: From Risk to EBITDA
Once you identify these gaps, you must quantify them. Security findings are often dismissed as "IT problems" rather than "deal problems." This is a mistake. Operational security gaps are MSP valuation factors that should drive purchase price adjustments.
We recommend categorizing findings into three buckets:
- Day 0 Remediation (Closing Conditions): Critical vulnerabilities (e.g., exposed RMM, no MFA on admins). These must be fixed before the wire is sent. There is no negotiation here.
- Day 100 CAPEX (Working Capital Adjustment): Tooling gaps. If the MSP is using legacy AV and needs to migrate 5,000 endpoints to CrowdStrike or SentinelOne, that is a hard cost. Calculate the license cost + implementation labor and deduct it from working capital or add it to the 100-day budget.
- Operational Opex (EBITDA Adjustment): If the MSP is understaffed and cannot meet patch SLAs without hiring two more security engineers, that is a permanent increase in COGS. This reduces pro-forma EBITDA and, by extension, the purchase price.
According to IBM’s Cost of a Data Breach Report 2024, the difference in breach costs between organizations with high vs. low security AI and automation adoption is nearly $2.2 million. If your target MSP relies on manual checks and spreadsheets, you are acquiring a $2.2 million liability waiting to happen.
Do not let the "Compliance Mirage" blind you. In MSP acquisitions, the paperwork is irrelevant if the RMM is exposed. Dig into the operational reality, quantify the security posture, and price the risk accordingly.