The $50M Black Box
The deal looked perfect on the surface. A B2B SaaS platform in the logistics space, $12M ARR, growing 20% YoY, with a healthy 25% EBITDA margin. For "Portfolio Paul," the Operating Partner leading the diligence, this was a standard add-on acquisition for a platform company. The Quality of Earnings (QofE) report was clean. The sales pipeline was validated. The legal team had flagged only minor IP concerns.
But the software itself—the asset Paul was about to buy for an 8x multiple—was a black box.
Traditionally, IT due diligence is a questionnaire. "Do you use AWS?" "Do you have a disaster recovery plan?" "Are you SOC 2 compliant?" The CTO answers "yes" to everything, and the deal moves forward. This "check-the-box" approach is the single largest destroyer of value in modern software acquisitions. It tells you about the infrastructure, but nothing about the asset.
We advised Paul to go deeper. We didn't want a questionnaire; we wanted a code audit. The target company pushed back—standard behavior for founders who know their closet is messy—but eventually granted read-only access to their repositories. What we found turned a "perfect" deal into a potential disaster, and ultimately, a masterclass in value preservation.
The Diagnostic: Converting "Spaghetti Code" to Dollar Signs
We ran a 5-Day Technical Due Diligence assessment. We weren't looking for "pretty code"—that doesn't exist in growing companies. We were looking for financial liability disguised as engineering complexity. We focused on three non-negotiable metrics:
1. The Cyclomatic Complexity of the "Crown Jewels"
We mapped the codebase and isolated the billing and routing engine—the core IP that justified the valuation. While the frontend looked modern, the backend core had a Cyclomatic Complexity score of over 50 (anything over 15 is hard to maintain; over 30 is dangerous). It was a tangled mess of nested logic written five years ago by a founder who was no longer technical. Translation: Any attempt to add new features to the core product would take 3x longer than industry benchmarks. The product roadmap the seller presented was mathematically impossible.
2. Code Churn vs. Throughput
We analyzed the git commit history. In the last six months, 33% of developer time was spent rewriting code that had been shipped less than three weeks prior. This wasn't innovation; it was remediation. The team was running on a treadmill, fixing breakage caused by a fragile architecture. McKinsey data suggests that tech debt can consume up to 40% of IT estate value; here, it was consuming a third of the payroll.
3. Open Source Risk (The Security Debt)
Finally, we scanned for dependencies. We found critical libraries that hadn't been updated in four years, containing known high-severity vulnerabilities (CVEs). To bring the platform into compliance with the buyer's security standards (and pass a future SOC 2 audit) would require a complete refactor of the authentication layer. IBM estimates the average cost of a data breach at $4.88M—a risk Paul was about to inherit for free.
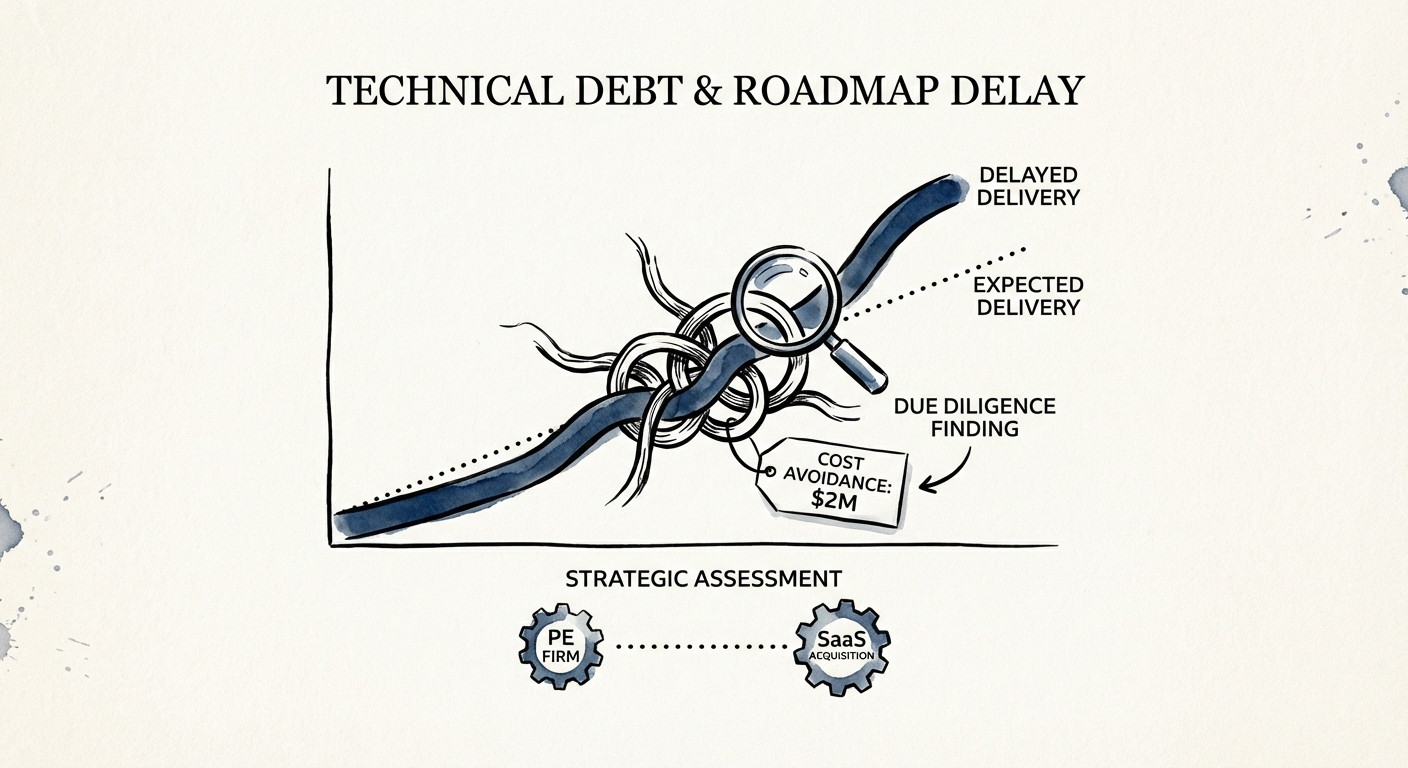
The Re-Trade: $2.1M in Remediation Costs
We didn't just hand Paul a report saying "the code is bad." We handed him a bill. We calculated the Remediation Cost required to stabilize the asset before it could support the growth thesis.
- Refactoring the Billing Engine: 3 Senior Engineers x 6 Months = $450k
- Security Remediation: Immediate 2-month sprint for the entire team = $300k
- Roadmap Delay Impact: The inability to ship the new "Enterprise Module" until Q3 (instead of Q1) due to debt paydown = $1.35M in delayed revenue and missed synergy capture.
Total Estimated Impact: $2.1M.
Paul took this data to the negotiation table. He didn't argue about code quality; he argued about CapEx requirements. He presented the technical debt as a deferred maintenance liability, identical to a leaking roof in a real estate deal.
The result? The seller conceded. The purchase price was adjusted downward by $2M to account for the immediate engineering investment required post-close. Paul didn't kill the deal—he de-risked it. By quantifying the technical debt, he ensured that his 100-day plan budget was funded by the seller, not his LP's capital.
The Lesson for Operating Partners
Stop treating codebases as black boxes. Technical debt is financial debt. If you don't find it in diligence, you will pay it off in EBITDA margin every month after the close. The goal isn't to find perfect code; it's to price the imperfections into the deal.