The Era of "Trust Me, It Works" Is Over
For the last decade, technical due diligence in the mid-market was often a formality. A CTO from the buying firm might glance at your architecture diagram, ask if you use AWS or Azure, and perhaps request a demo of your CI/CD pipeline. If the product worked and customers weren't churning en masse, you passed.
That era is dead. In 2026, Private Equity firms are no longer just buying revenue streams; they are buying code efficacy and platform scalability. They have been burned too many times by "black box" platforms that require a complete rewrite six months post-close.
Today, the due diligence process is forensic. Buyers are deploying automated code scanners like Black Duck and SonarQube before they even sign the LOI. They aren't looking for "best practices"—they are looking for liabilities. According to the 2025 Synopsys Open Source Security and Risk Analysis (OSSRA) report, 96% of audited codebases contained unpatched open source vulnerabilities, and 91% contained components that were more than four years out of date.
For a founder or CTO, this is a wake-up call. Your "working product" might be technically insolvent in the eyes of a sophisticated buyer. If your technical house isn't in order, one of two things will happen: the deal dies, or the buyer uses your technical debt to shave millions off the enterprise value. This isn't just an engineering problem; it's a valuation cap.
The Three Pillars of the Modern Technical Audit
When a PE firm sends in their technical operating partners (or a third-party firm like Crosslake or West Monroe), they are not interested in your roadmap features. They are investigating three specific risk vectors. If you want to survive the audit, you need to self-assess against these pillars today.
1. Intellectual Property & Open Source Compliance
This is the most common deal-killer. Buyers need to know: Do you actually own the code you are selling? In the rush to scale, engineering teams often pull in open-source libraries without tracking licenses. The risk of a "copyleft" license (like GPL) infecting your proprietary codebase is real.
The 2025 data is damning. Synopsys found that the average application contains over 500 open-source vulnerabilities. If a buyer finds evidence of strict copyleft licenses in your core IP, they may walk away immediately rather than risk a lawsuit. You must have a Software Bill of Materials (SBOM) ready before they ask.
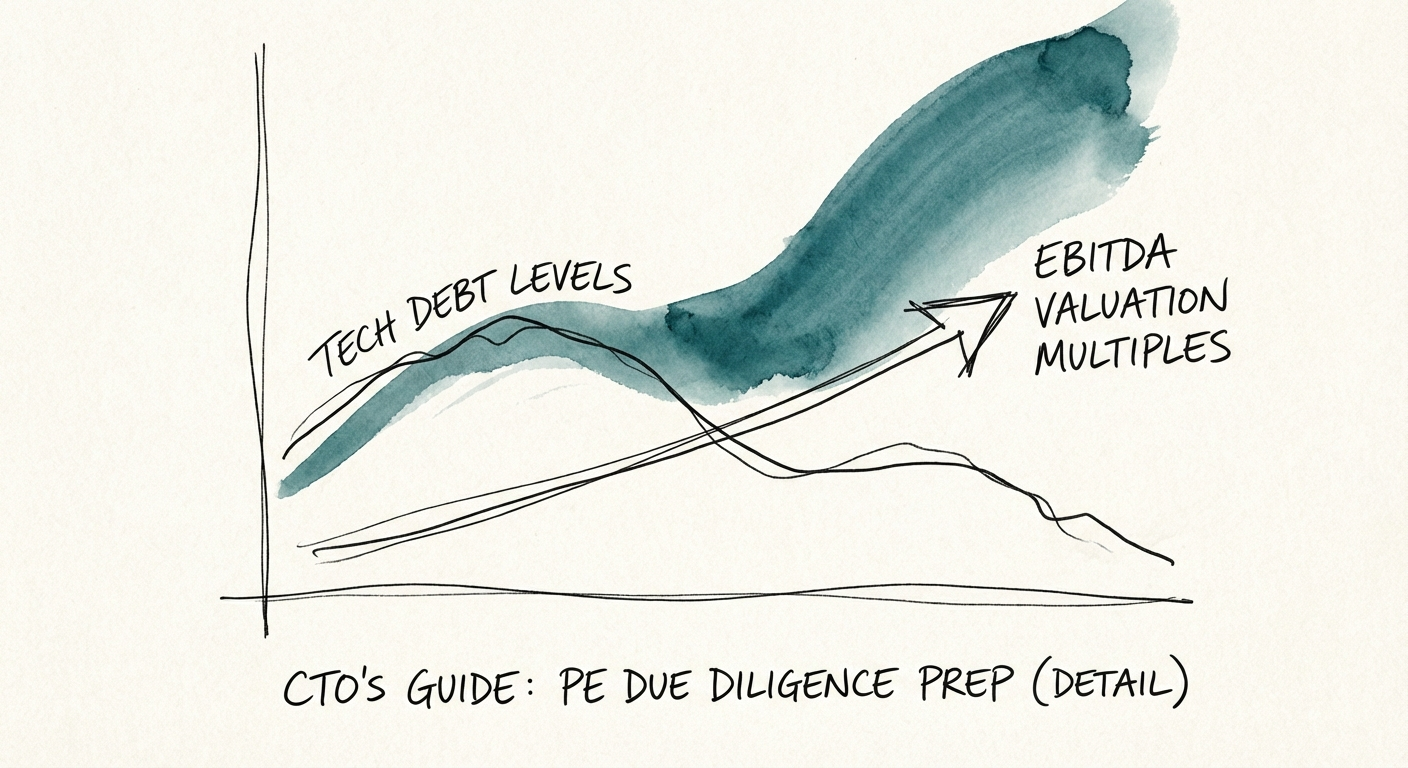
2. Technical Debt as a Financial Liability
Technical debt is no longer an abstract concept; it is being quantified as a deduction from EBITDA. Buyers calculate the "remediation cost"—the actual dollar amount required to bring your platform up to industry standards. McKinsey data suggests that technical debt consumes up to 40% of an organization's entire technology estate in stalled companies.
If your team spends 50% of their time on maintenance and bug fixes, the buyer sees that as a "scalability tax." They will argue that your projected growth margins are impossible without a massive injection of capital to fix the platform—capital that comes out of your exit price. See our guide on quantifying technical debt in M&A for the exact formulas they use.
3. Infrastructure Efficiency & Scalability
Gone are the days when "cloud-native" was enough. Now, buyers look at Unit Economics of Cloud Spend. If your AWS bill grows linearly with revenue, you have a margin problem. Elite SaaS firms decouple infrastructure cost from revenue growth. If your COGS (Cost of Goods Sold) for hosting is above 15-20% of revenue, you will be flagged as "architecturally inefficient."
The CTO’s Action Plan: From Liability to Asset
You cannot fix five years of technical debt in the 60-day exclusivity window. However, you can control the narrative and mitigate the red flags. Here is the 90-day prep guide for the exit-minded CTO.
- Run Your Own Scan First: Do not let the buyer be the first one to scan your code. Purchase a license for a tool like Synopsys or Snyk and run a full audit. Identify high-risk vulnerabilities and license conflicts. Remediation of critical security flaws is non-negotiable.
- Document the "Why": You will have tech debt. The difference between a red flag and a managed risk is documentation. Create a "Technical Debt Register" that lists known issues, their impact, and your plan to address them. This shows the buyer you are an operator, not a victim. Read 10 Red Flags in Technology Due Diligence to see what to prioritize.
- Standardize Your SDLC: If your deployment process relies on one "hero" engineer running scripts from their laptop, you have Key Person Risk. Document your Software Development Life Cycle (SDLC). Show that your delivery pipeline is automated, repeatable, and independent of any single individual.
- Prepare the Data Room: A chaotic data room signals a chaotic engineering culture. Organize your technical documentation: architecture diagrams, security certifications (SOC 2 is now table stakes—see our integration guide), disaster recovery plans, and your SBOM.
The Valuation Defense
Ultimately, the CTO's role in an exit is to defend the valuation. When a PE buyer claims it will cost $5M to fix your platform, you need the data to prove it will only cost $500k. You can only win that argument if you have the audits, the documentation, and the roadmap to back it up. In 2026, technical excellence is not just about code quality—it's about deal quality.