The Compliance Gap That Kills Returns
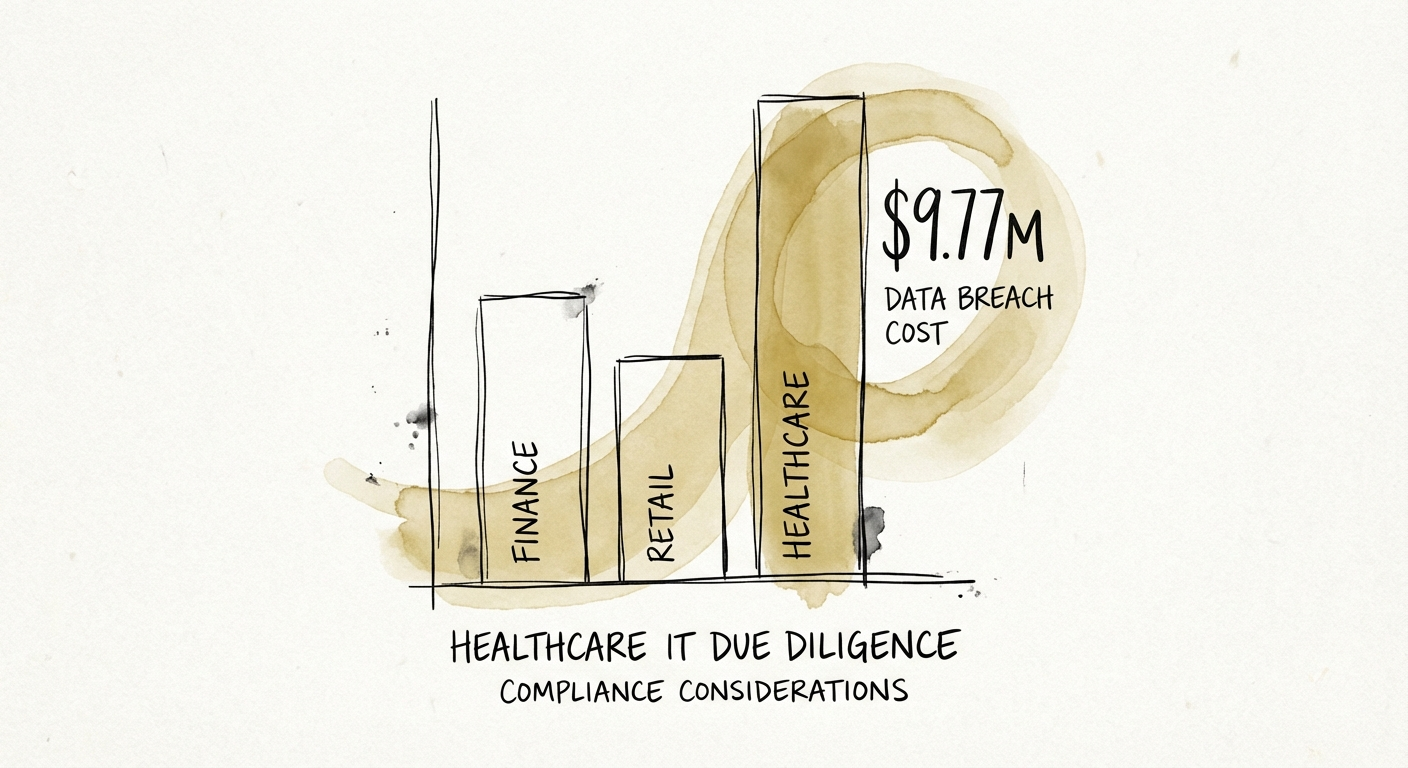
If you are looking at a healthcare asset in 2025, you are looking at the most expensive liability in the market. According to IBM’s 2024 Cost of a Data Breach Report, the average cost of a breach in healthcare has hit $9.77 million—nearly double the global average across other industries. For a Private Equity sponsor, this isn't just an operational headache; it is a direct hit to EBITDA and a potential wipeout of your equity check.
The problem is that most Founder-led healthcare SaaS or services companies treat compliance as a documentation exercise, not an engineering discipline. They show you a binders-worth of HIPAA policies, a clean SOC 2 Type I report, and a letter from a friendly auditor stating they are 'compliant.' Do not believe them.
In the last 18 months, I have audited dozens of healthcare targets that were 'paper compliant' but technically defenseless. They had policies against unauthorized access, but their database passwords were hardcoded in plain text. They had procedures for termination, but former employees still had active VPN keys. This gap—the delta between what the General Counsel says and what the code actually does—is where deal value evaporates.
For Portfolio Paul, the risk isn't just the fine; it's the remediation. Bringing a legacy healthcare platform up to modern security standards often requires a complete re-architecture, costing 15-20% of the initial investment thesis. If you don't catch this in diligence, that cost comes out of your value creation budget, not the purchase price.
The 'Risk Analysis' Trap: What OCR Is Actually Hunting
The U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR) has shifted its enforcement strategy. They are no longer just looking for lost laptops; they are hunting for Risk Analysis Failures. In recent 2024 and 2025 settlements, the #1 cited violation wasn't a hack itself, but the failure to conduct a thorough, accurate risk analysis before the breach occurred.
5 Technical Red Flags That Kill Deals
When my team performs technical due diligence on healthcare assets, we ignore the policy manuals and look at the infrastructure. Here are the five most common 'deal killers' we find in mid-market healthcare IT:
- The 'All-Access' Database: Founders often give developers production database access to fix bugs quickly. In a HIPAA environment, this is a ticking time bomb. If we see a single shared root password, we flag it as a critical severity finding.
- Unencrypted Data at Rest: Many 10-year-old Electronic Health Record (EHR) systems were built before transparent encryption was standard. Encrypting a 4TB database post-close isn't a weekend patch; it's a major migration that carries downtime risk.
- Missing MFA on VPNs: In 2025, if the target's remote access points do not enforce Multi-Factor Authentication (MFA), they are already breached. We assume compromise until proven otherwise.
- The 'Pixel' Problem: Recent class-action lawsuits have targeted healthcare providers using tracking pixels (like Meta Pixel) behind patient login walls. If your target marketing team is tracking user behavior on the patient portal, you might be buying a class-action lawsuit.
- Vendor Sprawl: The target claims compliance, but do they have Business Associate Agreements (BAAs) with every single API vendor they use? We often find 'shadow IT'—marketing tools or analytics platforms—that are ingesting PHI without a BAA in place.
These aren't just IT tickets. They are technical debt that must be quantified in dollars and deducted from the enterprise value.
The Operator's Action Plan: Retrade or Walk
You cannot 'fix' a culture of non-compliance in the first 100 days without significant capital. Your diligence must translate technical findings into financial terms. Here is how to handle the findings:
1. Quantify Remediation as Debt, Not Opex
Do not let the seller frame security upgrades as 'roadmap items.' If the platform is not compliant today, the cost to fix it is a debt-like item. If it costs $500k to encrypt the database and $200k to implement a SOC 2-ready logging system, that is $700k off the purchase price, dollar-for-dollar. Use our Technical Debt Quantification Framework to build this argument.
2. Demand a 'Technical' Reps & Warranties Carve-out
Generic R&W insurance often excludes known pre-existing conditions. If your diligence report highlights a lack of MFA, and you get breached via a credential stuffer in Month 3, your policy may not pay out. You need specific indemnification from the sellers for technical remediation costs incurred in the first 12 months.
3. The 100-Day Security Sprint
Post-close, you don't have time for a 12-month roadmap. You need a Security Posture Assessment immediately. Your CISO or interim security lead must lock down identity (MFA), isolate the backups (immutable storage), and segregate the network. Everything else is secondary.
Conclusion
In healthcare private equity, you are buying data, and that data is toxic if mishandled. The highest multiples in 2026 will go to firms that can prove 'Security by Design,' not just 'Compliance by Binders.' Don't buy the liability; buy the platform, and price the risk.