The 'Grand Rewrite' Fallacy vs. The Valuation Reality
In the high-stakes environment of 2026 M&A, technical debt is no longer just an engineering nuisance; it is treated by acquirers as an off-balance-sheet liability. Private Equity firms now deploy sophisticated automated code scanners (like Black Duck and SonarQube) during the exclusivity period, often uncovering liabilities that lead to a 10-15% 're-trade' on the final purchase price.
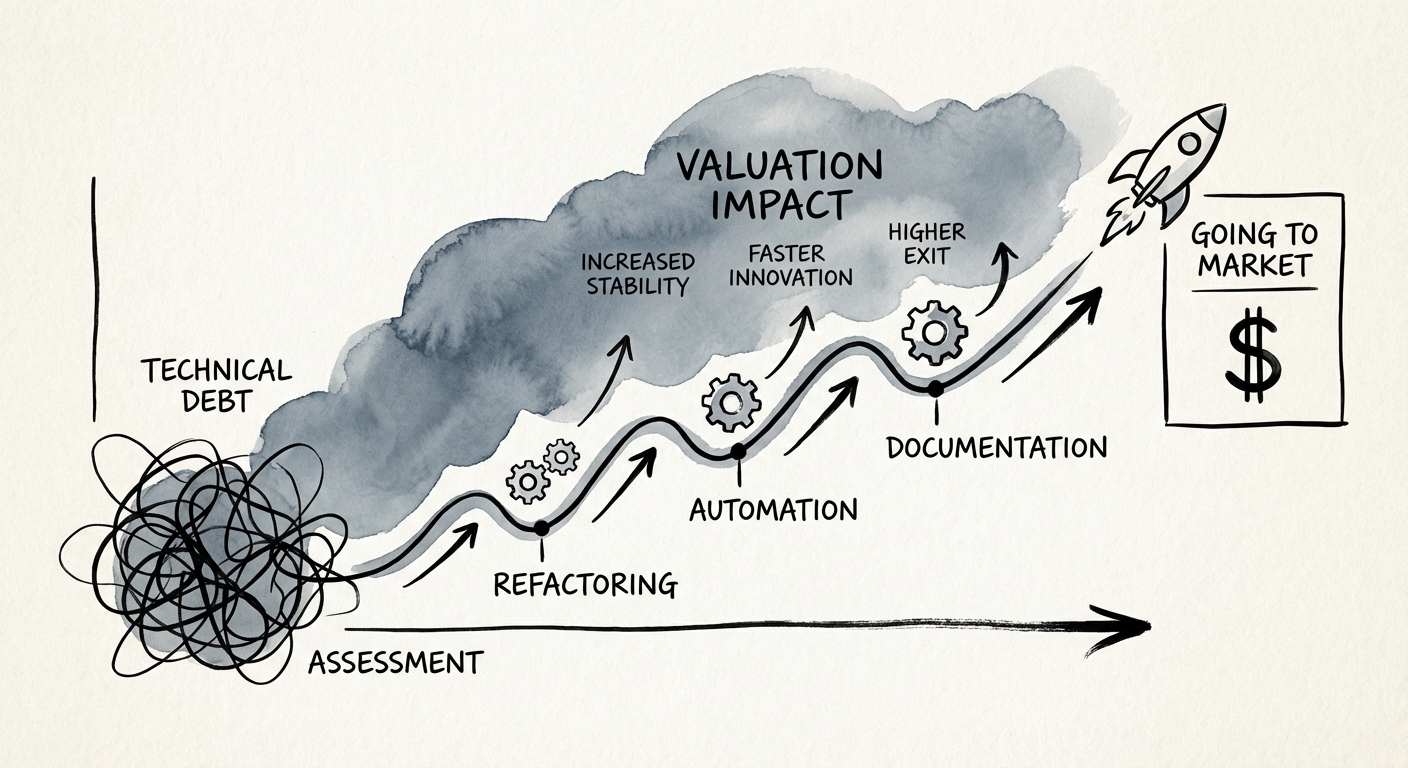
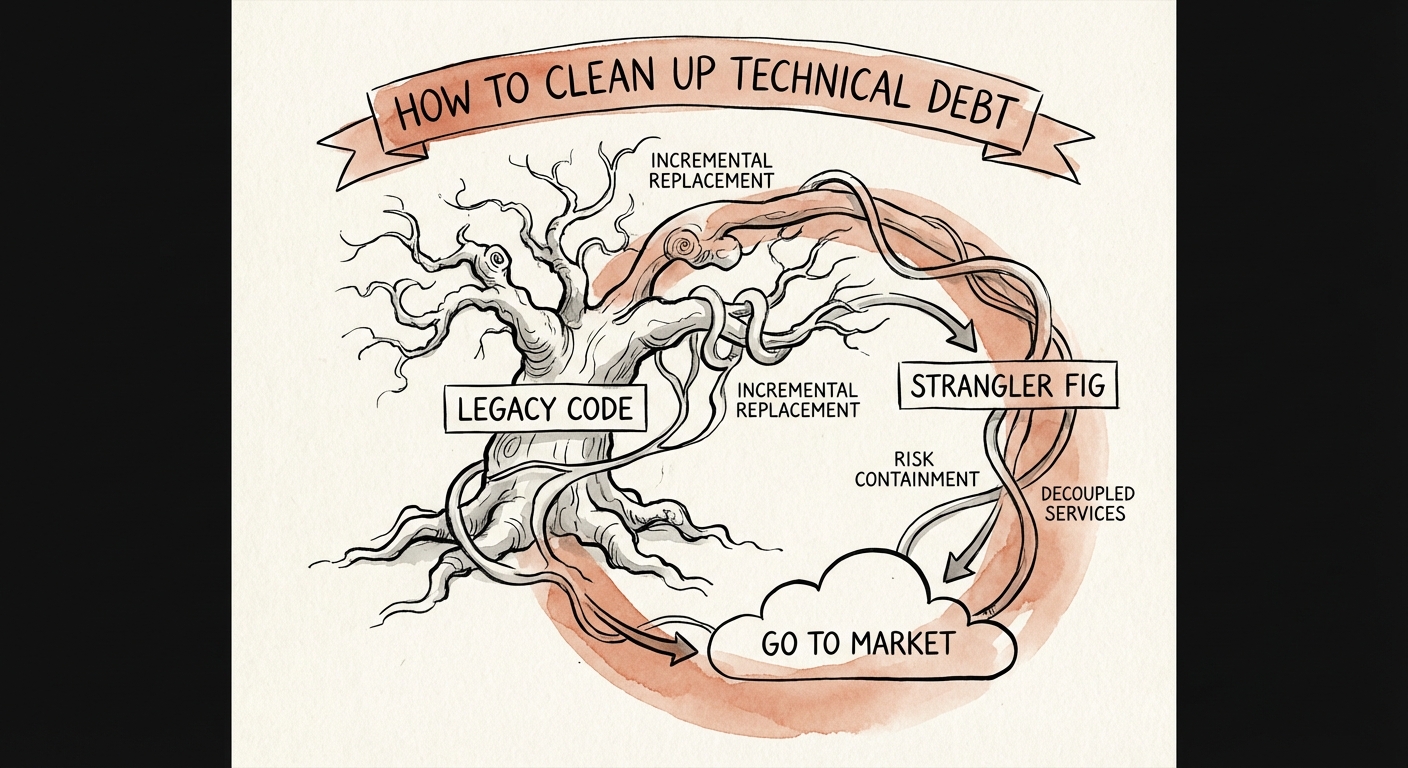
For Founders and CEOs, the instinct is often to authorize a 'Grand Rewrite'—a complete overhaul of the legacy codebase to make it pristine for buyers. This is a strategic error. Rewrites introduce new bugs, stall feature development, and rarely complete on time. As detailed in our Technical Debt Remediation Roadmap, the goal of pre-exit cleanup is not perfection; it is risk containment.
Buyers are not looking for elegant code; they are looking for predictability. They want assurance that the platform won't collapse when they double the user base, and that they won't be sued for open-source license violations. Your remediation strategy must shift from 'paying down interest' to 'eliminating deal-breakers.'
The 3 Red Flags That Kill Deals (And How to Spot Them)
Before you open your data room, you must audit your technology stack with the same rigor a buyer will. A proactive diagnostic prevents the buyer from discovering issues that you should have already disclosed or fixed. You can structure this using our Technical Due Diligence Report Template to mirror what their auditors will look for.
Focus your remediation efforts on these three critical categories:
- 1. Security & Compliance (The 'Hard No'): Active CVEs (Common Vulnerabilities and Exposures) in your third-party libraries are immediate deal stoppers. Buyers assume that if you haven't patched a known vulnerability, you have been breached. Remediation: Automated dependency updates and a documented patch management process.
- 2. Intellectual Property Risk (The 'Valuation Killer'): The presence of 'copyleft' open-source licenses (like GPL) in your proprietary codebase can technically force you to open-source your IP. This destroys asset value instantly. Remediation: Scan all libraries now. Replace or isolate incompatible licenses immediately.
- 3. Scalability Bottlenecks (The 'CapEx Trap'): If your architecture relies on a single monolithic database that is nearing vertical scaling limits, the buyer sees a $2M re-platforming project. Remediation: You don't need to move to microservices, but you must demonstrate a viable path to horizontal scaling, even if it requires 'sharding' data logic.
The 6-Month Remediation Sprint
Once you have identified the red flags, execute a containment strategy. This is a finite, 6-month sprint designed to ring-fence liability without halting your roadmap.
Month 1-2: Triage and Documentation
Fix critical security flaws immediately. For architectural debt that cannot be fixed quickly, document it. Buyers will forgive a known issue with a documented mitigation plan; they will punish an 'unknown' risk. Use the Cost of Delayed Remediation Formula to show the board why this prioritization protects exit value.
Month 3-4: The 'Strangler Fig' Pattern
Instead of rewriting legacy modules, wrap them in APIs. This allows you to build new features in a modern stack while leaving the stable, legacy code untouched but contained. This demonstrates to buyers that you have a 'modernization pattern' in place.
Month 5-6: The 'Clean Build' Validation
Ensure your build and deployment pipeline is fully automated. If a buyer's technical team cannot build your software from a clean repository in under an hour, they will assume your engineering velocity is inflated. Automation is the ultimate proof of operational maturity.