The Great Bifurcation: Log Management vs. Threat Defense
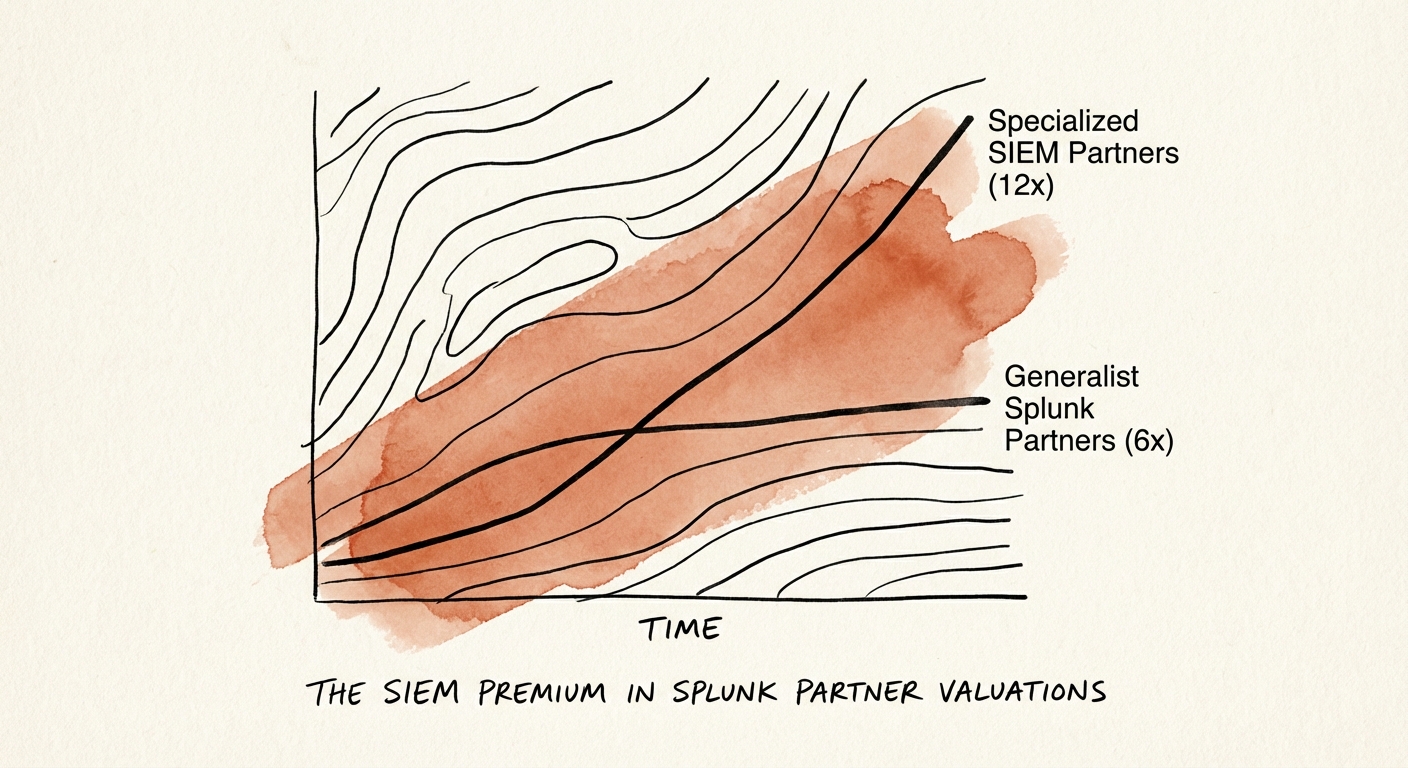
In the wake of Cisco’s $28 billion acquisition of Splunk, the partner ecosystem has bifurcated into two distinct asset classes with vastly different valuation profiles. On one side are the Generalist Observability Partners (the ‘Log Managers’), who primarily focus on infrastructure monitoring, IT operations, and basic log aggregation. These firms trade at standard IT services multiples of 6x to 8x EBITDA. Their revenue is often project-based, tied to ‘lift and shift’ cloud migrations or basic dashboarding, which—while necessary—is increasingly commoditized by lower-cost competitors and automated observability tools.
On the other side are the Specialized Security Partners (the ‘Threat Defenders’). These firms have built deep expertise around Splunk Enterprise Security (ES), SOAR (Security Orchestration, Automation, and Response), and Mission Control. Unlike their generalist peers, they don’t just ‘ingest data’; they interpret risk. Private equity buyers and strategic acquirers (including global systems integrators and specialized MSSPs) are currently paying a premium for this capability, driving multiples to 12x to 14x EBITDA.
Why the Gap Exists
The valuation gap stems from switching costs and revenue quality. A dashboard monitoring server CPU usage can be replaced by Datadog, Dynatrace, or New Relic with relative ease. However, a Splunk Enterprise Security implementation that powers a Global 2000 Security Operations Center (SOC)—complete with custom correlation searches, risk-based alerting (RBA), and automated response playbooks—is the digital nervous system of the enterprise. It is incredibly sticky, mission-critical, and resistant to ‘rip and replace’ campaigns. For acquirers, this ‘defensive moat’ justifies the 4-turn premium.
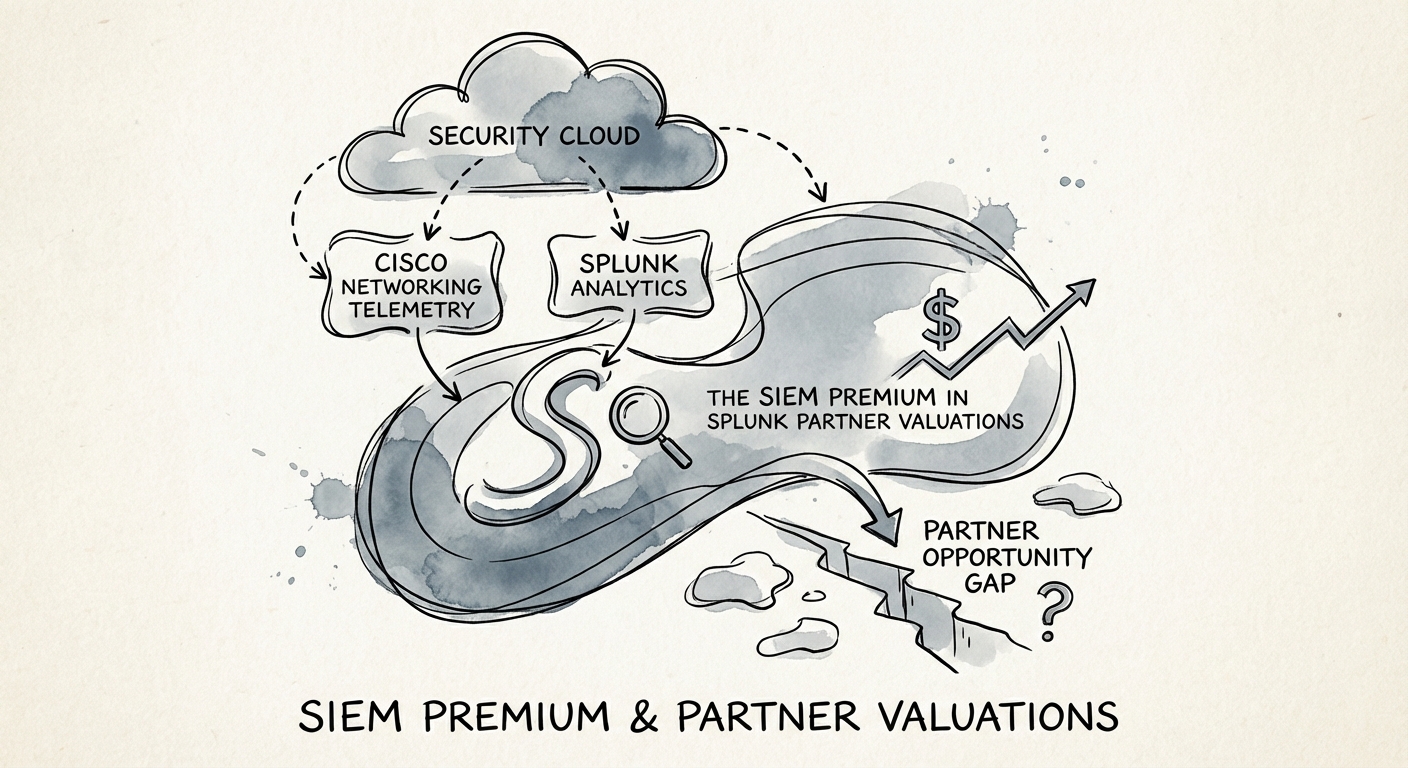
The Cisco Catalyst: 'Security Cloud' and the M&A Ripple Effect
The Cisco acquisition has accelerated this valuation divergence. Cisco’s strategy revolves around the ‘Security Cloud,’ integrating network telemetry (Cisco) with data analytics (Splunk). Partners who can bridge this gap—combining network security engineering with data-driven threat detection—are becoming scarce assets. This scarcity is driving a ‘talent premium’ for firms that possess verified expertise in both domains.
Furthermore, the market is seeing a consolidation trend where ‘pure-play’ MSSPs (Managed Security Service Providers) are acquiring Splunk consultancies to acquire their engineering talent. These acquirers are not looking for general ‘Splunk Architects’; they are hunting for engineers who understand Risk Based Alerting (RBA) and Threat Intelligence Platform (TIP) integration. If your firm’s ‘security practice’ consists merely of installing the ES app without customizing the detection logic, you will fail technical due diligence, and your multiple will revert to the generalist mean.
The Recurring Revenue Multiplier
The most valuable Splunk partners have pivoted from ‘time and materials’ implementation to Managed Detection and Response (MDR) models. By wrapping proprietary content (e.g., industry-specific threat detection rules) and 24/7 monitoring around the Splunk platform, these firms generate high-margin recurring revenue (60%+ Gross Margin) compared to the lower-margin professional services (35-45% Gross Margin) of implementation shops. In 2026 M&A, a dollar of MDR EBITDA is worth roughly 1.5x to 2x a dollar of project-based EBITDA.
The 'Paper Tiger' Trap: Due Diligence Red Flags
For investors and founders, distinguishing between a true SIEM specialist and a ‘Paper Tiger’ is critical. A ‘Paper Tiger’ is a partner that holds the requisite certifications (e.g., Splunk Certified Security Consultant) but lacks the operational maturity to deliver ‘outcomes.’ In due diligence, we often see these firms claiming ‘Security DNA’ because they have deployed Splunk ES for clients. However, upon code audit, we find default correlation searches enabled, excessive false positives, and no custom content. This is not a security practice; it is software resale with a services wrapper.
True SIEM value is demonstrated through:
- Custom Content Libraries: Proprietary detection rules mapped to MITRE ATT&CK frameworks that go beyond ‘out of the box’ defaults.
- Automation Maturity: Measurable reduction in Mean Time to Respond (MTTR) for clients via SOAR playbooks.
- Retention Rates: Net Revenue Retention (NRR) above 115% for managed security clients, indicating that the service is indispensable.
If you are a founder looking to exit, you must audit your own practice before a buyer does. Are you selling ‘Splunk hours,’ or are you selling ‘Risk Reduction’? The answer determines whether you exit at 6x or 12x.