The 'Double-Pay' Paradox in Cybersecurity Consolidation
The strategic logic of 'Platformization'—Palo Alto Networks' (PANW) term for consolidating disparate security vendors onto their Strata, Prisma, and Cortex stacks—is irrefutable. For a Private Equity sponsor, the math is seductive: replace 15 expensive point solutions (CrowdStrike, Splunk, Zscaler, Check Point) with a single, integrated platform agreement. The projected result is a 30% reduction in Total Cost of Ownership (TCO) and a unified security posture.
But the operational reality in 2026 is often a P&L disaster we call the "Double-Pay Paradox."
According to 2025 market data, while 80% of organizations have a stated goal of vendor consolidation, 51% are actually increasing their vendor count. Why? Because they buy the platform but fail to operationalize the exit from their legacy tools. They sign a multi-million dollar NGS (Next-Gen Security) credit agreement with PANW, but they lack the operational process to decommission the old estate.
The result is not savings; it is cost layering. Your portfolio company is now paying for Cortex XSIAM and Splunk. They are paying for Prisma Access and Zscaler. They are paying for Cortex XDR and CrowdStrike. Instead of an EBITDA uplift, you have created a cash flow drain that persists for 18 to 24 months, eroding the very deal value the project was meant to unlock.
Diagnostic: 3 Signs Your Platformization Project Is Stalling
How do you know if your portfolio company is falling into this trap? Look for these three operational red flags in your board reporting.
1. The 'Credit Hoarding' Warning
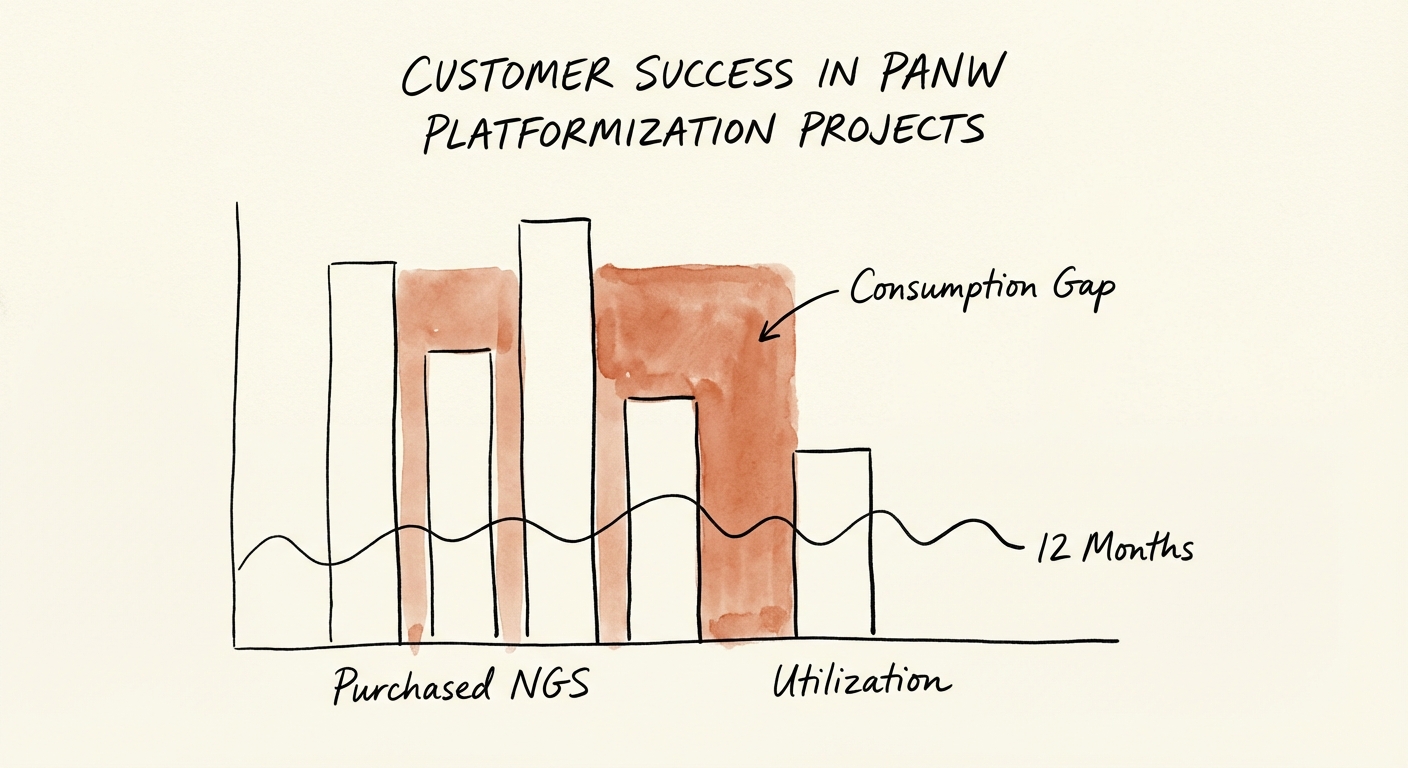
Palo Alto Networks increasingly sells via 'NGS Credits'—a prepaid currency for consuming software capabilities. In a healthy deployment, credit consumption tracks linearly with the deployment plan. If your CFO reports that 60% of year-one credits are still unconsumed in Month 9, you don't have a technical problem; you have a deployment process failure. It means the team has bought the shelf space but hasn't moved the inventory. This is often due to a lack of documented migration procedures that paralyze the engineering team.
2. The 'Feature Parity' Stalemate
Operational teams often stall migrations because they are waiting for 'feature parity' between the old point solution and the new platform. This is a false target. The value of a platform is not that it does every single niche thing the old tool did; it's that the integration provides 72 days faster incident identification (according to IBM/PANW data). If your CISO is delaying the shutdown of a legacy tool because of a minor feature gap, they are prioritizing comfort over risk reduction and EBITDA.
3. The 'Firewall Fallacy'
In network security (Strata), a common failure mode is treating a migration like a hardware refresh. Engineers 'lift and shift' the old port-based policies from a Check Point or Cisco ASA firewall into the PANW environment without adopting 'App-ID' (application-based policies). This is like buying a Ferrari and towing it with a mule. You are paying the premium for a Layer-7 security platform but operating it as a Layer-3 packet filter. The result? No visibility gain, no security improvement, and no justification for the spend.
The Fix: Process Documentation as a Migration Accelerator
The difference between a project that stalls and one that delivers a 101% ROI lies in process rigor, not technical brilliance. To fix a stalled platformization project, you must shift focus from 'installing software' to 'retiring capabilities.'
First, mandate a Legacy Decommissioning Roadmap. Do not track the project by 'percentage of PANW installed.' Track it by 'percentage of legacy spend turned off.' This aligns the technical team's incentives with the investment thesis.
Second, require your partners to bring transferable process documentation. A generic VAR (Value Added Reseller) will ship you the licenses and wish you luck. A strategic partner will provide the 'runbooks' for replacing a SIEM with XSIAM or swapping EDR agents without breaking production. As we've noted in The Transferability Premium, acquirers pay for turnkey operations, not heroics.
Finally, look for partners who understand the specialized nature of these migrations. As detailed in The SecOps Specialist Premium, firms that specialize in security operations command higher multiples because they drive outcomes, not just volume. Don't let your 'generalist' IT provider manage a Tier-1 security transformation.