The 32% Margin Leak You Can't See on the P&L
If you are reviewing a CIM (Confidential Information Memorandum) for a SaaS platform built on Google Cloud, the COGS line is lying to you. In 2025, 32% of cloud spend is wasted annually, according to the Flexera State of the Cloud Report. For a target company with $5M in annual hosting costs, that is $1.6M of potential EBITDA leakage masquerading as "necessary infrastructure."
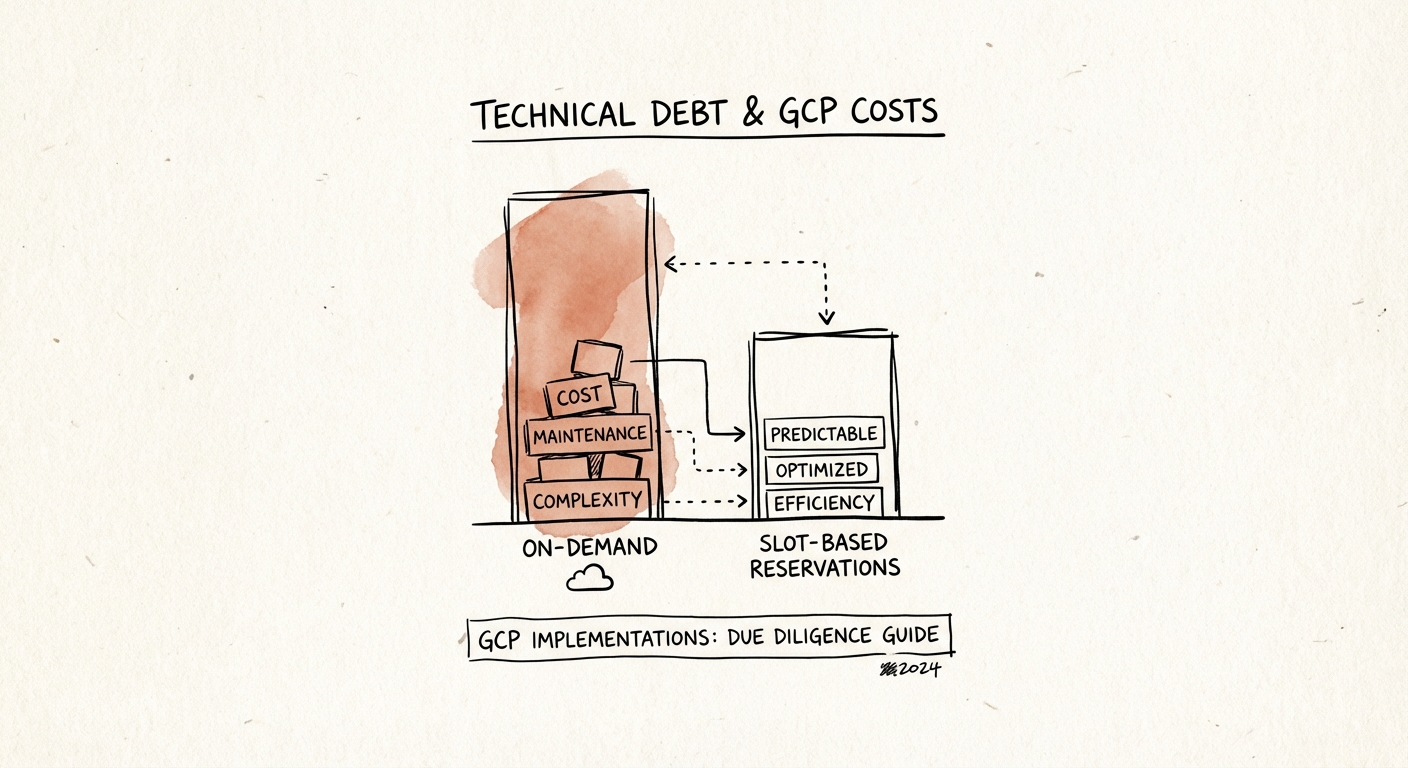
Most Private Equity operating partners treat cloud bills as fixed costs. They aren't. They are variable costs dictated by architectural discipline. When a portfolio company lifts and shifts legacy code into GCP without refactoring, they aren't just inefficient—they are actively destroying exit value. We call this the "GCP Tax."
This isn't about code quality; it's about financial engineering. Technical debt in the cloud is just high-interest financial debt that doesn't show up on the balance sheet until you try to scale. Here is how to find it during your 10-day technical due diligence window.
1. The "ClickOps" Liability: Manual Console vs. Terraform
The first question your technical diligence team must ask is: "How is infrastructure provisioned?"
If the answer is "we log into the Google Cloud Console and click create," you are buying a liability, not an asset. This practice, known as "ClickOps," guarantees that the environment is unrepeatable, undocumented, and fragile. In a disaster recovery scenario, a ClickOps environment cannot be restored quickly, posing a massive business continuity risk.
You want to see Infrastructure as Code (IaC), typically Terraform. If the target has 90% coverage of their environment in Terraform, that infrastructure is an asset—it can be audited, versioned, and replicated. If they have 0% coverage, you need to budget $250k-$500k in post-close CapEx to remediate it. This is a direct valuation haircut you should negotiate before signing.
The BigQuery Money Pit: "Select *" Is Killing Your Gross Margin
Startups love BigQuery because it is serverless and infinitely scalable. That is also why it bankrupts them. Unlike traditional SQL databases where you pay for storage capacity, BigQuery charges by the amount of data processed per query.
In sloppy engineering cultures, developers write queries that scan terabytes of data to answer simple questions (the infamous SELECT *). I recently audited a Series C SaaS company where a single dashboard widget was costing $4,000 per month to render because of poor partitioning and clustering strategies.
The Audit Step: Request a localized export of the billing data for BigQuery grouped by "User" and "Query." If the top 10% of queries are consuming 80% of the spend, you have a remediation opportunity. This is "low-hanging fruit" for value creation—fixing these queries can often drop COGS by 15-20% in the first 90 days. But if you don't catch it in diligence, you're just paying the bill.
GKE Sprawl: The "Always On" Tax
Google Kubernetes Engine (GKE) is the gold standard for container orchestration, but it encourages over-provisioning. Engineers tend to request resources for "peak load" that never happens. We frequently see GKE clusters running at 12-15% CPU utilization while the company pays for 100%.
During diligence, ask for a report on cluster utilization vs. request limits. If the gap is wider than 40%, you are looking at pure waste. This isn't just optimization; it's about rightsizing the asset base you are acquiring.
Security Debt: The "Owner" Role Time Bomb
Financial debt has interest; security debt has potential foreclosure. In GCP, the most common form of security debt is IAM (Identity and Access Management) bloat.
In early-stage companies, it is convenient to give developers the "Owner" or "Editor" role. This is the digital equivalent of giving every employee the master keys to the bank vault. In a recent diligence screen, we found 42 users with "Owner" privileges in a company with only 30 engineers (contractors had never been offboarded).
This is a deal-killer for sophisticated enterprise buyers (the people you want to sell this asset to in 3-5 years). Remedying IAM debt is painful, slow, and risky—it often breaks production applications. If you see widespread use of primitive roles (Owner/Editor/Viewer) instead of custom, least-privilege roles, you must factor a 6-month security remediation project into your 100-day plan.
The Re-Trade Leverage
Don't just note these findings in a report. Price them.
1. ClickOps: $300k deduction for Terraform implementation.
2. BigQuery Waste: Adjust EBITDA add-backs for "non-recurring" cloud waste (if you can prove it's remediable).
3. IAM Bloat: Increase the integration budget for security hardening.
You aren't just buying code; you're buying the machine that runs the business. Make sure it isn't burning cash faster than it prints it.

