Founders routinely authorize $35,000 for a penetration test without realizing that 80% of these engagements are nothing more than glorified, automated vulnerability scans wrapped in a custom PDF. We see this margin-crushing mistake constantly during the exit preparation phase. You stroke a check to a boutique cybersecurity firm, receive a 40-page document filled with "critical" findings that are actually false positives, and assume you have checked the compliance box. But when you enter private equity due diligence, the buyer's operating partner will immediately spot the deception, and your perceived security maturity will collapse, taking a massive chunk of your valuation with it.
In our last engagement preparing a $40M SaaS platform for market, we had to throw out a $25,000 "pentest" report just three weeks before going to market. The buyer's technical due diligence team would have instantly identified it as a raw Nessus automated scan masked as manual exploitation—a discrepancy that routinely triggers a 15% valuation holdback. The vendor had simply run a scripted tool, branded the output with their logo, and charged a premium enterprise rate for zero actual security value. This is the dirty secret of the mid-market penetration testing industry, and it preys entirely on founders who lack the technical translation to challenge the SOW.
There is a massive, highly consequential chasm between vulnerability scanning and manual penetration testing. As defined by the Cybersecurity and Infrastructure Security Agency (CISA), true penetration testing requires human intelligence to chain vulnerabilities, bypass controls, and demonstrate actual business impact. An automated tool can tell you if your server is missing a patch. It takes a human operator to realize that an authenticated user can manipulate a hidden URL parameter to view another tenant's billing data. If your vendor turns the report around in 48 hours, you are buying a scan, not a test.
Where the $15k-$60k Actually Goes
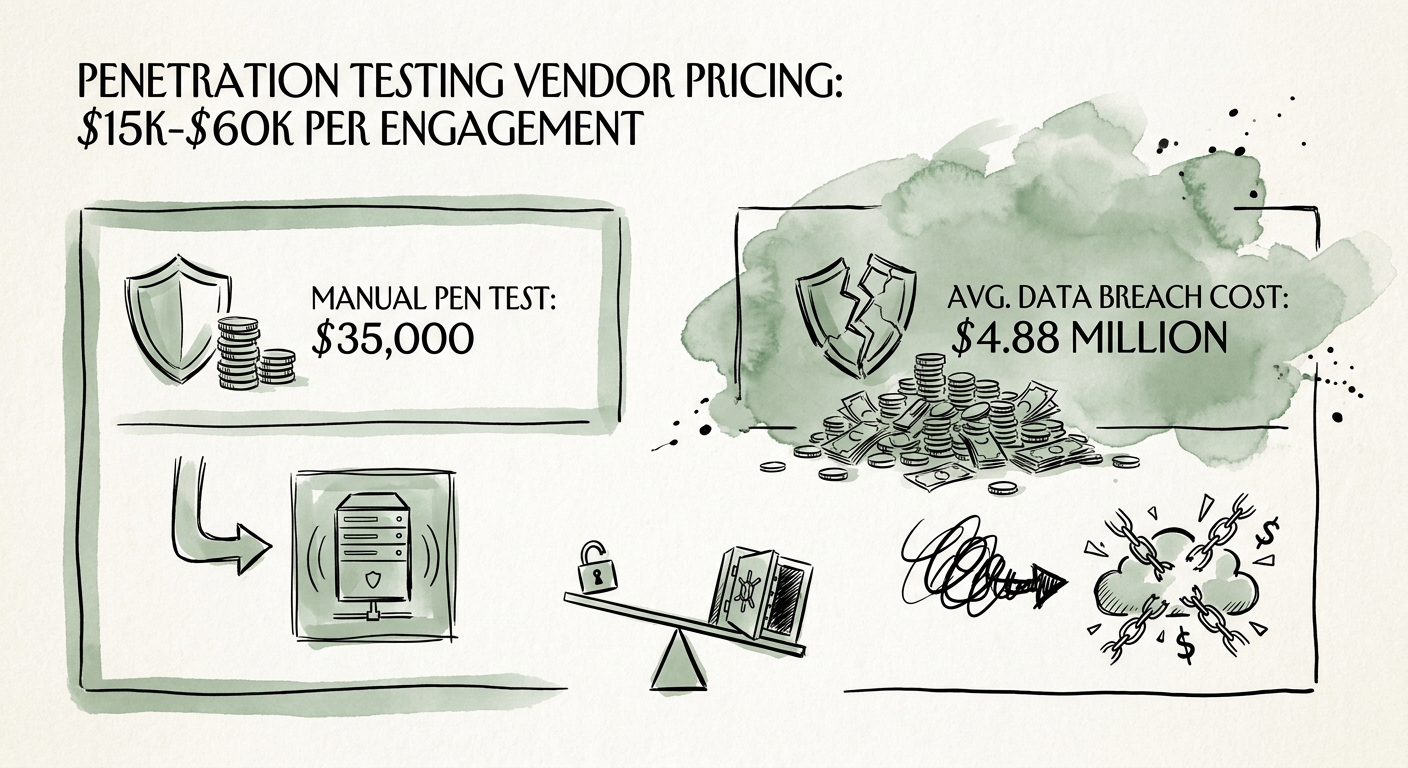
When you budget for a legitimate penetration test in 2026, the pricing benchmarks are stark and unforgiving. A true, manual, grey-box web application penetration test for a mid-market SaaS company starts at a hard floor of $15,000. If you are paying anything less than that, you are likely funding the vendor's software licensing fees rather than buying senior engineering time. For complex platforms with sophisticated role-based access control (RBAC), multi-tenant architectures, and extensive REST or GraphQL API integrations, that number scales rapidly to the $40,000 to $60,000 range per engagement.
The core driver of this cost is human expertise. Skilled ethical hackers who can manually exploit business logic flaws are expensive, scarce, and constantly poached by the world's largest tech firms. They do not just identify a cross-site scripting (XSS) vulnerability; they write the custom payload to exfiltrate a session token, proving exactly what an attacker could steal. We tell our portfolio companies to view this expense not as an IT line item, but as fundamental enterprise risk mitigation. According to the IBM Cost of a Data Breach Report, the average cost of a breach now sits at a staggering $4.88 million. Against that devastating baseline, a $35,000 manual penetration test is simply the cheapest insurance policy your board can buy.
Furthermore, do not conflate basic compliance readiness with actual cyber resilience. Many founders purchase a low-tier pentest solely to satisfy an auditor and accelerate their SOC 2 certification timeline. While a $5,000 scan might get you past a generic compliance audit, it will completely disintegrate under the scrutiny of a sophisticated acquirer. Buyers are paying 12x to 15x multiples for your intellectual property; they demand undeniable proof that your application layer is hardened against targeted, human-led attacks.
How PE Buyers Evaluate Your Penetration Test
Private equity buyers do not just read the executive summary of your penetration test—they relentlessly dissect the methodology. The first thing a technical due diligence team checks is the ratio of automated findings to manual exploits. If every finding in your report is a generic CVE (Common Vulnerabilities and Exposures) related to legacy SSL configurations or missing HTTP headers, the acquirer knows you have never been truly tested. They view this as a massive red flag that your engineering team operates in a vacuum.
Real threats to SaaS valuations live in the business logic, not in unpatched server software. The Verizon Data Breach Investigations Report (DBIR) consistently highlights that web applications are the primary attack vector for systemic breaches, with attackers specifically targeting authentication bypasses and privilege escalation paths. These are exactly the vulnerabilities that automated scanners miss, and exactly the fundamental flaws that manual penetration testers are hired to find. If your testing history lacks documented attempts at tenant isolation breaches, API manipulation, or lateral movement, the buyer will assume your platform is compromised and discount the deal accordingly.
To protect your valuation and your technical credibility, you must redefine how you procure these services. First, demand a strict methodology breakdown in the vendor's Statement of Work (SOW), explicitly forbidding them from passing off raw automated scan results as the final deliverable. Second, require a designated retest clause. A professional cybersecurity firm will include remediation verification within their standard $15k-$60k fee structure, allowing your engineers to patch the critical flaws and receive a clean bill of health before opening the data room. Taking absolute control of this process is an essential part of your security posture assessment and ensures your M&A exit remains on track without devastating, last-minute valuation haircuts.

