The $3M Blockage
The call came on a Tuesday. It was the CEO of a Series B SaaS company in our portfolio. They had missed their Q3 forecast, not because of product fit or sales execution, but because three enterprise deals—totaling $3M in annual contract value (ACV)—were stuck in "Security Review."
The procurement teams at these Fortune 500 prospects had sent over 200-question spreadsheets. The first question on every sheet was: "Do you have a current SOC 2 Type II report?"
The answer was no.
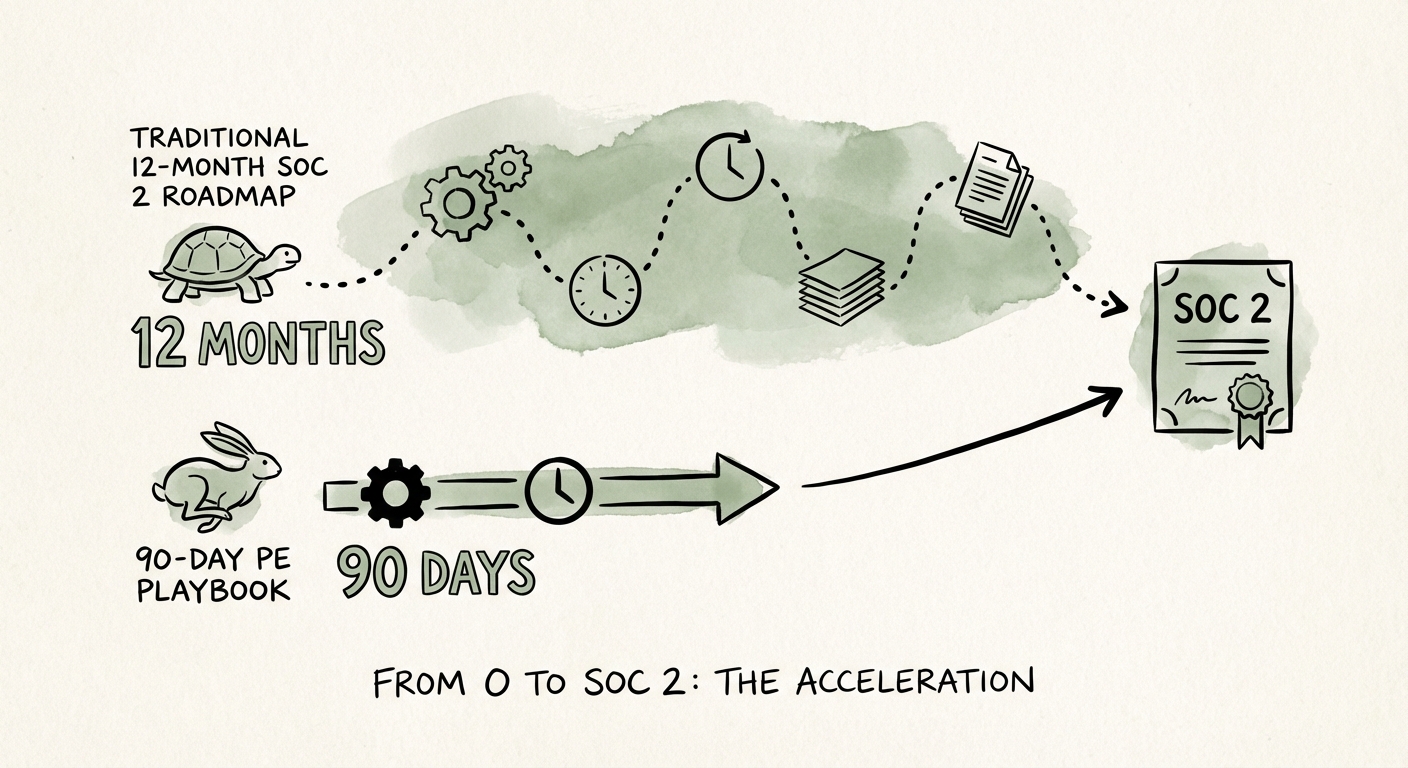
The standard consulting playbook says SOC 2 takes 9 to 12 months. You hire a firm, they interview your team, they write policies, you implement controls, and then you wait for a 6-month observation period. In Private Equity, we don’t have 12 months. We often don't even have six. If we waited the standard timeline, those $3M in deals would be dead, churned to a competitor with a badge on their footer.
We needed a different playbook. We needed to get from zero to a report in hand within a single quarter. We didn't need to cut corners; we needed to engineer the process with the same rigor we apply to EBITDA expansion. Here is exactly how we executed a 90-day SOC 2 acceleration program.
The Acceleration Framework: Systems, Not Heroes
Speed in compliance usually implies sloppiness. In our case, speed came from scope reduction and automation. We treated the SOC 2 audit not as a consulting project, but as an engineering sprint.
1. The "Snapshot" Strategy (Type 1 vs. Type 2)
The biggest misconception in PE operations is that you need a Type 2 report to close a deal. You don't. You need a SOC 2 report. A SOC 2 Type 1 report verifies that your controls are designed correctly at a specific point in time. It is a snapshot. A Type 2 verifies they have been operating effectively over time (usually 3-12 months).
The Play: We targeted a Type 1 report immediately. This took 90 days. We handed that report to the enterprise buyers to prove our design was secure, while simultaneously triggering the start of our Type 2 observation window. This satisfied the vendor risk management requirements for 100% of the stalled deals.
2. Automate the Evidence (The "Cheat Code")
Traditional audits involve screenshots. Thousands of them. Sysadmins taking screenshots of firewall rules, HR taking screenshots of onboarding tickets. This manual evidence collection accounts for 60% of the timeline.
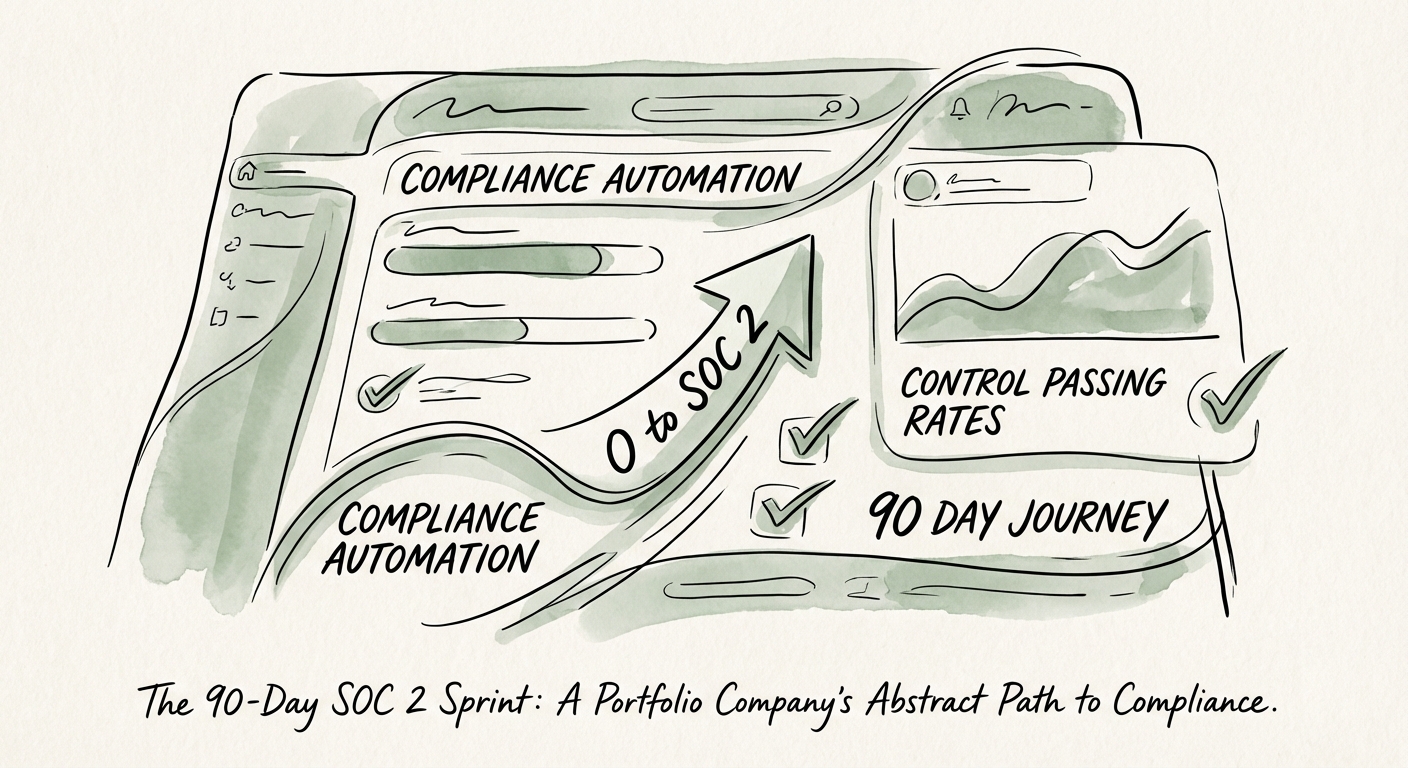
We deployed a compliance automation platform (Drata) on Day 1. We integrated it with the company’s AWS, GitHub, Google Workspace, and Jira instances. Within 48 hours, the platform automatically pulled evidence for 70% of the controls. Instead of asking "Do you encrypt databases?" and waiting for an email, the system queried the AWS API and marked the control as "Passing" or "Failing" instantly.
3. The Two-Week Remediation Sprint
The automation revealed gaps immediately. We didn't have MFA on all root accounts. We didn't have formal code review gates in GitHub. Instead of a 3-month "policy writing" phase, we ran a 2-week engineering sprint. The mandate was simple: Fix the red dots on the dashboard.
- Week 1: Access Control (MFA, SSO enforcement, offboarding former employees).
- Week 2: Infrastructure Security (Encryption at rest, logging enabled, backup verification).
4. Policy Templates, Not Novel Writing
Engineers hate writing policy documents. Consultants love charging you to write them. We skipped both. We used pre-approved, auditor-vetted policy templates provided by the automation platform. We customized the variables (Company Name, CTO Name) and adopted them. Total time: 3 days. Value preserved: $20,000 in consulting fees.
The Financial Impact: Compliance as a Multiple Expander
On Day 88, the auditor issued the SOC 2 Type 1 report. On Day 91, the sales team forwarded the report to the three stalled enterprise prospects. Two of them signed within the week. The third signed the following month. That’s $3M in ARR unblocked.
But the real value wasn't just the closed deals. It was the valuation defense.
Paying Down "Compliance Debt"
In due diligence, lack of compliance is treated as debt. If I’m buying a company without SOC 2, I’m modeling in the cost and risk of achieving it. I might compress the multiple or demand a higher escrow. By achieving SOC 2, this portfolio company removed a massive red flag from their future data room.
Furthermore, because we kept the automation platform running, the company is now in "continuous compliance." The Type 2 audit next year won't be a fire drill; it will be a non-event. The system is monitoring the controls 24/7/365.
The Operator's Lesson
If your portfolio company is stalled by security questionnaires, do not accept the "it takes a year" excuse. That is the consulting answer. The operator answer is that compliance is a data problem, and data problems can be automated. You can speak fluent EBITDA and fluent DevOps simultaneously—and when you do, you close deals faster.