The Liability Shift: Why 'Trusting the CISO' is Now Negligence
For decades, the standard for board oversight of technology was plausible deniability. If the CISO said, "we are secure," and the Audit Committee minuted it, the board had fulfilled its fiduciary duty. In 2025, that defense officially died.
Two regulatory earthquakes have shifted the ground under directors' feet. First, the SEC's Regulation S-K Item 106 now mandates that public companies (and by extension, the private equity portfolios aiming to sell to them) explicitly disclose their processes for assessing, identifying, and managing material risks from cybersecurity threats. The 4-day disclosure clock for material incidents (Form 8-K Item 1.05) means you no longer have weeks to craft a narrative. You have 96 hours to tell the market—and your acquirers—exactly how bad the damage is.
Second, and more dangerously for individual directors, is the evolution of Caremark claims. The SolarWinds derivative litigation opened the door for shareholders to sue directors personally for "bad faith" oversight failures. If a board allows management to present "check-the-box" compliance while ignoring systemic technical debt or known vulnerabilities, that is no longer just a business failure; it is a potential breach of the duty of loyalty. As a PE Operating Partner, your risk isn't just a valuation haircut anymore; it's a direct legal exposure for your appointed directors.
The Qualified Technology Expert (QTE) Gap
While 86% of companies now disclose some form of cybersecurity expertise on their boards, the definition of "expertise" is often dangerously loose. A retired CEO who sat on a tech committee is not a QTE. In the eyes of regulators and sophisticated acquirers, a QTE must have direct, operational experience managing complex technical architectures. If your board lacks this specific competency, you are flying blind into a storm of technical liability.
The 3-Part Governance Diagnostic
To move from passive observation to active oversight, PE sponsors must restructure their board agendas. The era of the 15-minute annual "Cyber Update" is over. Effective governance now requires a specific, metric-driven interrogation of the technology stack. We recommend a three-part diagnostic framework to determine if your portfolio company is truly protected or merely lucky.
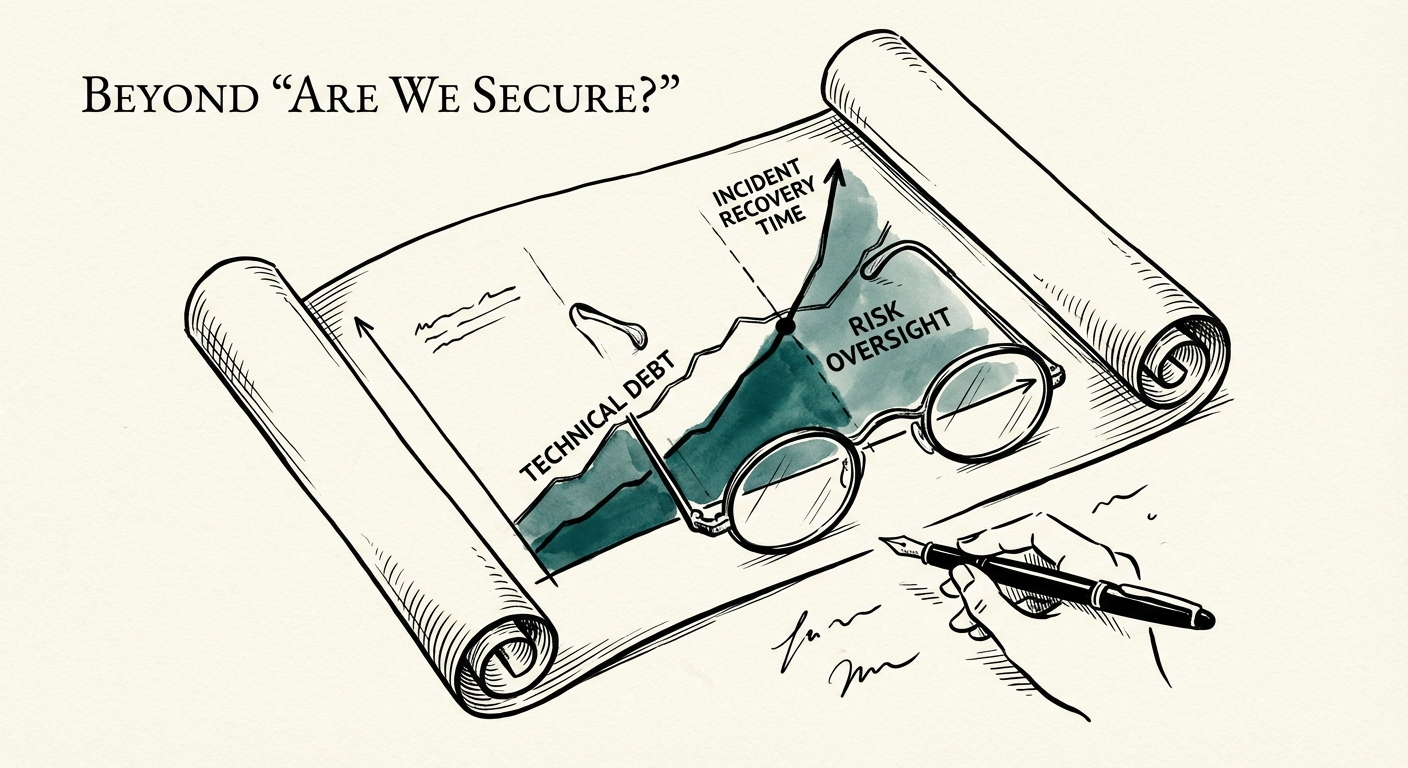
1. Strategic Alignment: Is Tech Debt a Solvency Risk?
Most boards view technical debt as an engineering annoyance. You must view it as a solvency risk. Ask your CTO to quantify technical debt not in lines of code, but in remediation dollars and risk exposure. If a critical legacy system cannot be patched because the code is too brittle, that is a measurable financial liability that must be booked against the company's enterprise value. If 30% of your engineering capacity is consumed by "keeping the lights on" (KTLO), your growth thesis is mathematically impossible.
2. Operational Resilience: The 'Mean Time' Litmus Test
Stop asking "How many attacks did we block?" That is a vanity metric. The only metrics that matter to a board are Mean Time to Detect (MTTD) and Mean Time to Recover (MTTR). If your CISO cannot answer these immediately, you do not have a security program; you have a firewall and hope. World-class organizations operate with an MTTR of under 4 hours for critical systems. If your portfolio company takes 4 days to recover, you are not just losing revenue; you are likely triggering material disclosure requirements that will scar the brand permanently.
3. Governance Rigor: The Independent Validation
Does your CISO report to the CIO? If so, you have a structural conflict of interest. The person responsible for building faster (CIO) should not be the boss of the person responsible for building safer (CISO). We advise our PE clients to enforce a dotted-line reporting structure where the CISO has a direct channel to the Risk Committee, independent of the CIO and CFO. Furthermore, rely on third-party technical due diligence not just at entry, but as an annual audit function.
5 Metrics Your Board Must Track Quarterly
You cannot manage what you do not measure, and you cannot govern what you do not understand. Replace the generic "Red/Yellow/Green" heatmaps with these five hard metrics to enforce accountability.
- Patch Latency: What is the average time (in days) between a critical patch release and its deployment across 100% of the estate? Anything over 14 days is negligence.
- Technical Debt Ratio: (Cost to Fix / Total Development Cost). If this ratio exceeds 20%, you are eroding equity value.
- Privileged Access Coverage: What percentage of administrative accounts are protected by Multi-Factor Authentication (MFA) and managed via a PAM (Privileged Access Management) solution? The answer must be 100%. No exceptions for "legacy systems."
- Phishing Susceptibility Rate: Not just the click rate, but the reporting rate. A culture of security is defined by how many employees report a suspicious email, not just how many avoid clicking it.
- Drill Success Rate: When was the last full-scale disaster recovery simulation? Did it meet the Recovery Time Objective (RTO)? If the answer is "we haven't tested it this year," assume the backup fails.
The role of the board is not to write code, but to ensure that the code is not a liability. By shifting the conversation from "trust" to "verification," you protect not just the asset, but your reputation as a fiduciary. For a deeper dive on what to report, review our guide on board reporting metrics that actually matter.