The most expensive line of code in your next acquisition isn’t legacy technical debt—it is a free, copied-and-pasted GPLv3 library that legally forces your target to open-source its entire $50 million proprietary platform.
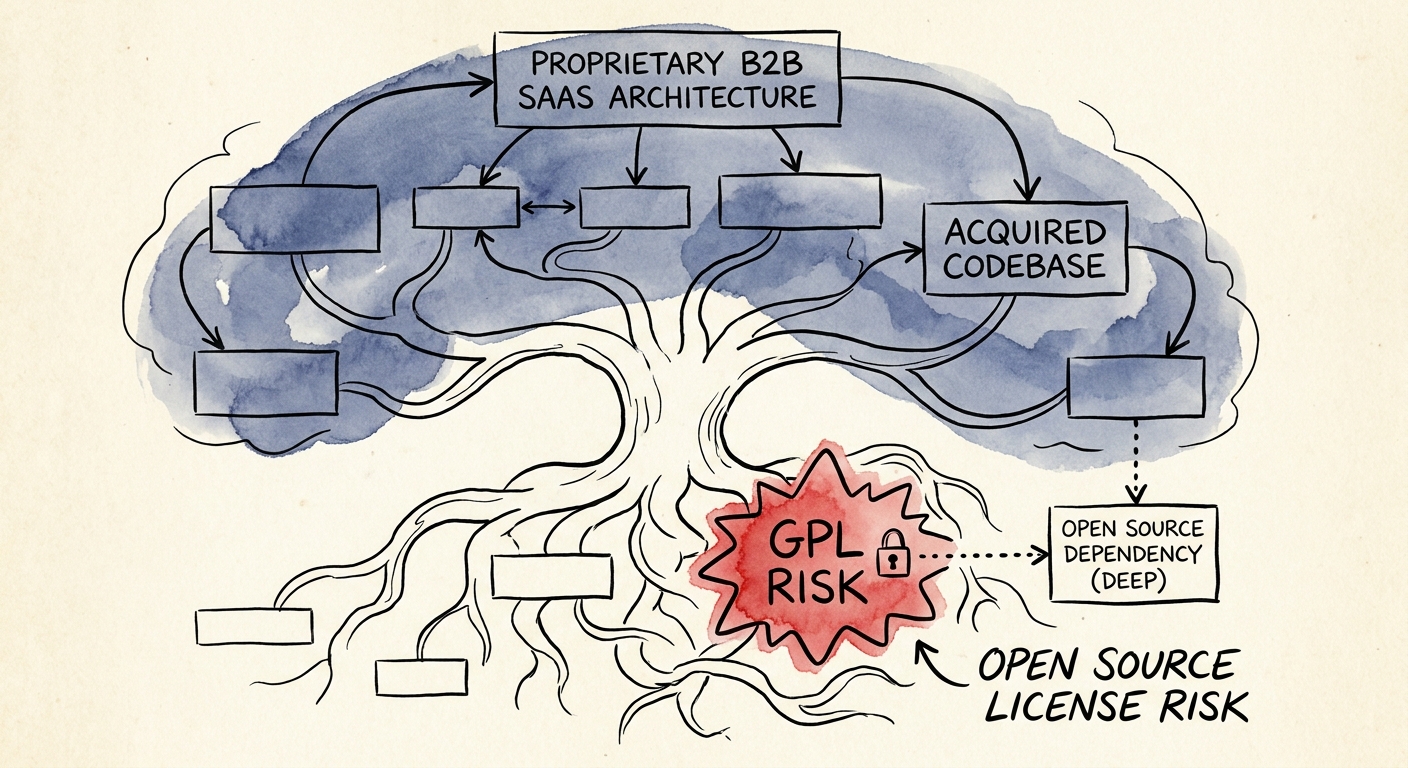
We are operating in an era where software development is essentially component assembly. Engineers do not write cryptography libraries or data visualization grids from scratch; they pull them from GitHub and npm. While this accelerates product velocity, it injects severe intellectual property risk directly into the core of your target's valuation. In our last engagement reviewing a $120 million B2B SaaS carve-out, we uncovered three instances of GPLv2 components deeply embedded in the target's core billing engine. Because these components were statically linked to the proprietary code, the viral or copyleft nature of the General Public License dictated that the entire billing engine must be distributed under the same open-source terms. The founders thought they owned $120 million in enterprise value; legally, they owned a public utility.
The data on this exposure is stark. According to the 2025 Synopsys Open Source Security and Risk Analysis (OSSRA) report, 96% of all commercial codebases contain open-source components, and a staggering 54% of those codebases contain active license conflicts. These are not minor compliance hiccups. When private equity sponsors buy software companies, they are buying the exclusive right to monetize proprietary intellectual property. If that intellectual property is polluted by a restrictive copyleft license like GPL, LGPL, or AGPL, the fundamental premise of the transaction evaporates.
Founders consistently dismiss this risk, assuming that because their software is delivered as a service (SaaS), distribution clauses do not apply. They are wrong. The Affero General Public License (AGPL) was specifically designed to close the SaaS loophole, explicitly triggering the copyleft provision even when software is merely accessed over a network. This is precisely why we flag AGPL exposure as an absolute deal-breaker in our 10 Red Flags in Technology Due Diligence That Kill Deals diagnostic. If your technical diligence stops at assessing architecture scalability and ignores software composition, you are walking directly into an IP landmine.
Furthermore, standard representations and warranties in your Purchase Agreement will explicitly state that the target company owns or has valid licenses for all intellectual property required to operate the business. A GPL violation immediately breaches these representations. When we audit codebases for mid-market sponsors, we find that the average engineering team has zero visibility into their transitive dependencies. A developer pulls in a benign MIT-licensed package, completely unaware that this package relies on a deeply buried GPLv3 library. The legal contagion spreads regardless of intent. You do not get a pass because the infringement was buried four layers deep in a dependency tree.
The Mechanics of the Copyleft Trap
To understand why this destroys enterprise value, you must understand the mechanical difference between permissive and copyleft licenses. Permissive licenses—like MIT, Apache 2.0, and BSD—allow you to use, modify, and distribute the code without forcing your proprietary additions into the public domain. They are commerce-friendly. Copyleft licenses—specifically the GPL family—operate on a philosophy of enforced software freedom. If you modify or link to a GPL component and distribute your software, your entire application becomes a derivative work and must also be licensed under the GPL.
This creates a horrific remediation timeline during due diligence. When we identify a GPL violation a week before the expected close, the deal stops. You cannot simply delete the offending file and move on. The target's engineering team must rip out the open-source component and either build a proprietary replacement from scratch or find a commercially licensed alternative. According to Revenera's latest State of the Software Supply Chain report, unearthing and remediating a critical license violation delays M&A transactions by an average of 4.2 weeks. In the current interest rate environment, a one-month delay kills the deal entirely as financing terms expire.
The SaaS Exemption Illusion
The most dangerous hallucination among technical founders is the belief that SaaS architecture neutralizes GPL risk. The traditional GPLv2 triggers upon the distribution of the software. Because SaaS companies host their software and customers only interact with the interface, founders argue no distribution takes place. This defense is legally precarious and technically fragile. First, if your target company deploys on-premise agents, mobile applications, or downloadable client tools that interact with the SaaS platform, distribution absolutely occurs. Second, the AGPL explicitly eliminates the distribution requirement. If your application contains AGPL code and users interact with it over a network, you must make your source code available.
This is why understanding exactly how software is compiled and delivered is critical. As outlined in our guide on How to Audit a Codebase in 5 Days, the distinction between dynamic linking and static linking is often the only barrier between a clean intellectual property profile and a complete loss of exclusivity. Private equity operating partners must demand a granular map of how third-party code integrates with the proprietary core. Accepting a verbal confirmation from the target's CTO that they only use standard open source is institutional negligence.
The 2026 Mandate: Software Bill of Materials (SBOM)
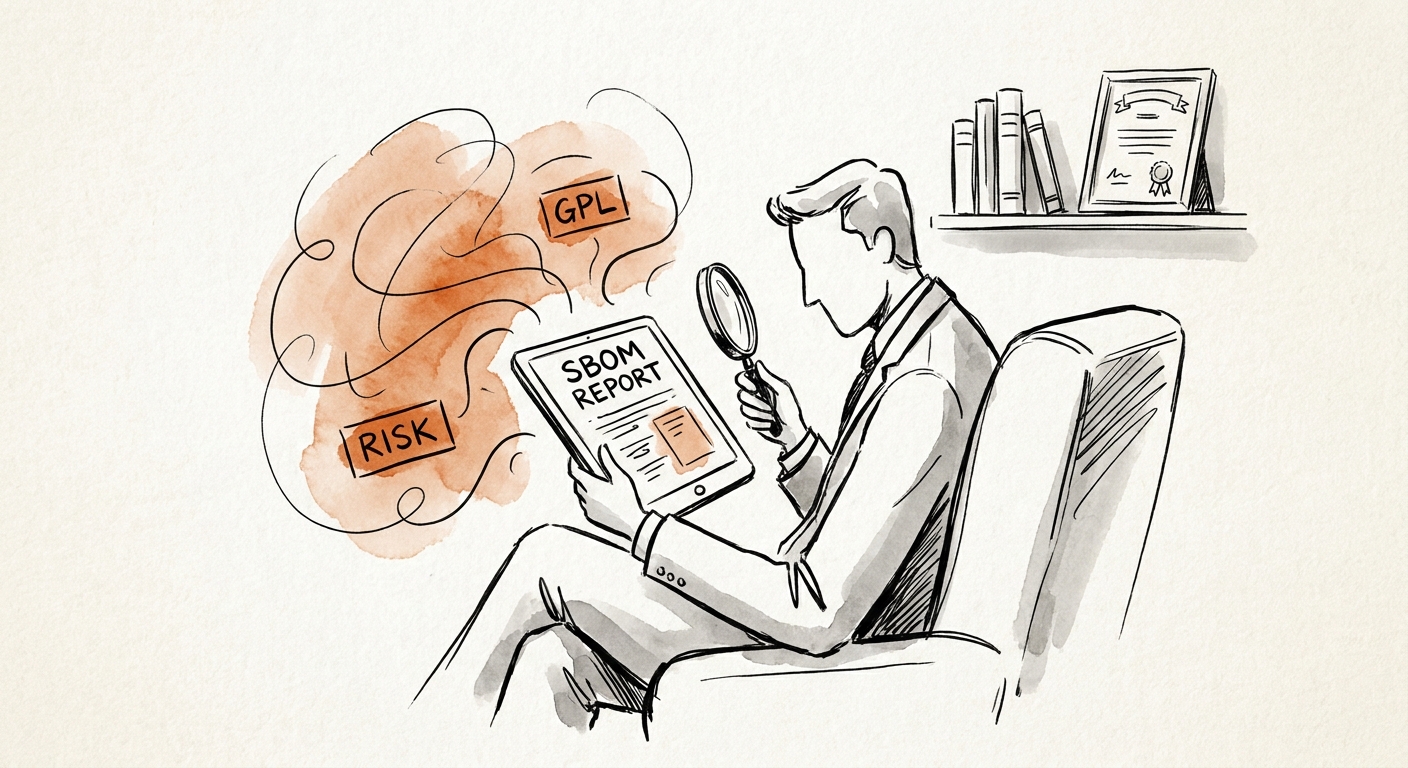
We do not rely on developer honesty; we rely on cryptographic proof. The standard for technical due diligence in 2026 requires the automated generation and analysis of a Software Bill of Materials (SBOM). An SBOM is a comprehensive, machine-readable inventory of every software component, library, and transitive dependency within a codebase, mapping each artifact to its specific licensing terms.
If a target company cannot produce an accurate SBOM within 24 hours of your data room request, their engineering governance is broken. According to Gartner research mandates, the majority of enterprise procurement teams now demand an SBOM before signing a software contract. If your target is selling to the Fortune 500 without one, their revenue is artificially fragile, and their ARR will collapse the moment a sophisticated enterprise buyer audits their supply chain. As we document in The 'Silent Deal Killer': Intellectual Property Documentation Requirements for Tech M&A, an absent SBOM is a direct indicator of undocumented contingent liabilities.
The Remediation Playbook for Sponsors
When you uncover restrictive license exposure in due diligence, you must execute a strict, three-step remediation playbook. First, quantify the operational dependency. Determine exactly what the offending code does. Is it a generic PDF generation library, or is it the core machine learning algorithm driving the product's value proposition? Second, establish the replacement cost. Require the target's engineering team to scope the exact sprint capacity required to rewrite or replace the component. Third, execute a dollar-for-dollar reduction in the purchase price, or establish a strict pre-closing covenant requiring the seller to remediate the violation at their expense before funds are wired.
Do not accept a post-closing escrow holdback for a severe GPL violation. Once you close the transaction, you own the legal liability. If an aggressive open-source copyright holder identifies the violation on day one of your hold period, your fund is the entity facing the injunction. The era of move fast and break things is over. In 2026, software is an assembled asset, and if you do not strictly audit the legal perimeter of the raw materials, you are buying a lawsuit, not a platform.