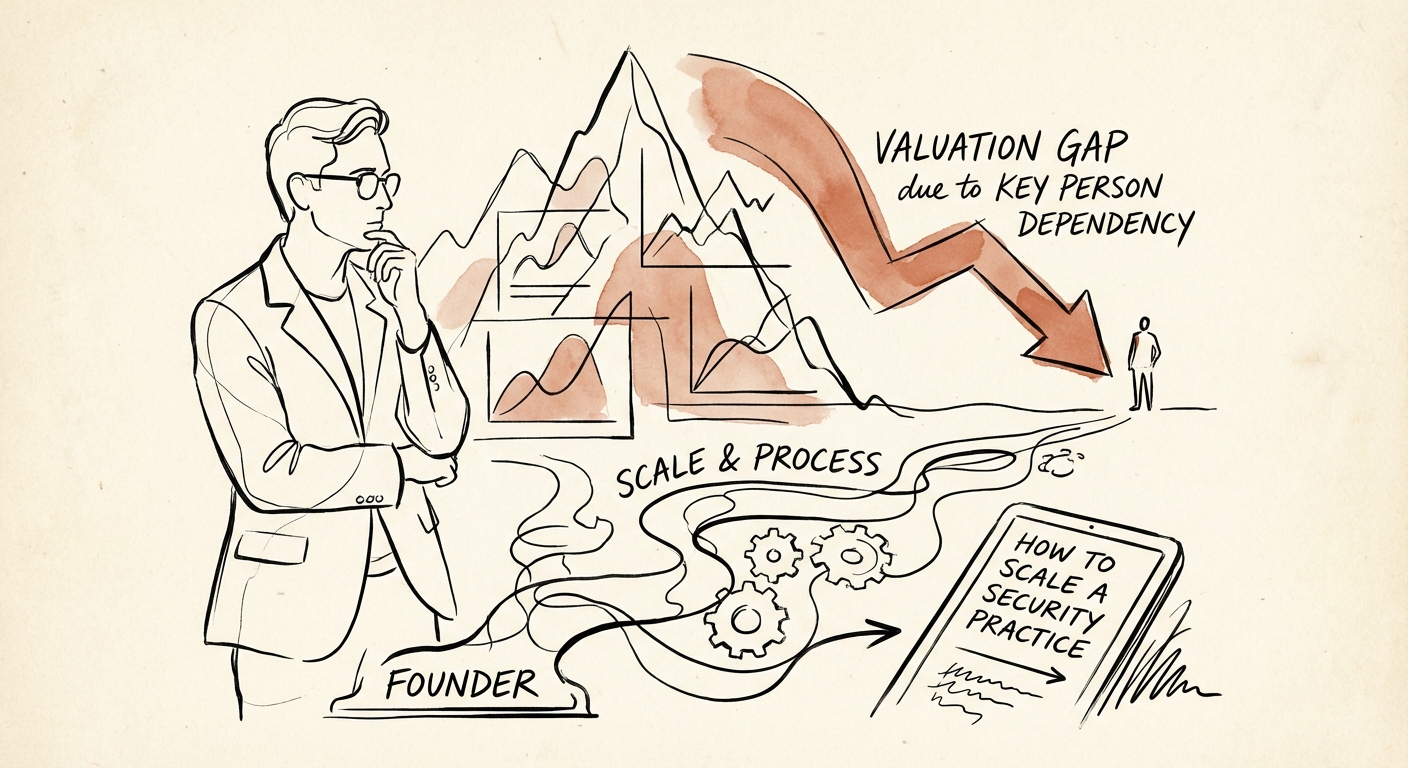
The High Cost of the 'Hero CISO'
In the early stages of a security practice, the founder is the product. Your personal reputation, your CISSP certification, and your late-night incident response heroics are what clients buy. This model works exceptionally well up to roughly $5M in revenue. However, as you approach $10M, this same asset becomes your practice’s greatest liability.
Data from 2025 M&A transactions reveals a stark reality: security practices with heavy founder dependency trade at a 30-50% discount compared to their systematized peers. While "platform" MSSPs are commanding 10x-15x EBITDA multiples, founder-reliant shops often struggle to break 4x-6x. Why? Because buyers aren't purchasing a business; they are purchasing a high-risk job description that no single employee can fill once you leave.
We call this the "Hero CISO" Trap. When every complex architecture decision, every high-stakes breach response, and every key sales meeting requires your personal presence, you haven't built a company; you've built a bottleneck. Private Equity investors view this as "Key Person Risk," and they price it aggressively. If the trust resides in you rather than the brand, the equity value is trapped in your head.
Diagnosing the Bottleneck: Why Security Firms Stall at $10M
The operational symptoms of founder dependency in security firms are distinct and measurable. If you are experiencing the following, you are likely hitting the "$10M Ceiling":
- The 'Besoke' Architecture Trap: Every client environment is a unique snowflake because you personally architected it. This prevents your team from using standardized playbooks, forcing you to troubleshoot every major issue.
- Sales Cycle Friction: Deals stall when you aren't in the room. Your sales team can open doors, but they can't close the "technical trust" gap without your validation.
- Utilization Drag: Your senior engineers are waiting for your approval on architectural reviews, causing billable hours to evaporate into administrative delays.
In 2025, the market has shifted towards Compliance-as-a-Service and automated MDR (Managed Detection and Response). Buyers and customers alike demand standardized outcomes, not artisanal consulting. If your delivery model relies on "founder intuition" rather than documented SOPs, you cannot scale. The "Hero" model essentially caps your growth rate at the speed of your own burnout.
The Valuation Impact of Standardization
Consider two security firms with $12M revenue. Firm A delivers custom security consulting led by the founder. Firm B sells a standardized "vCISO in a Box" subscription delivered by a team using a unified tech stack. In due diligence, Firm A is valued at ~1x Revenue (a services multiple). Firm B is valued at ~2.5x Revenue (a recurring revenue multiple). The difference isn't the revenue; it's the transferability of that revenue.
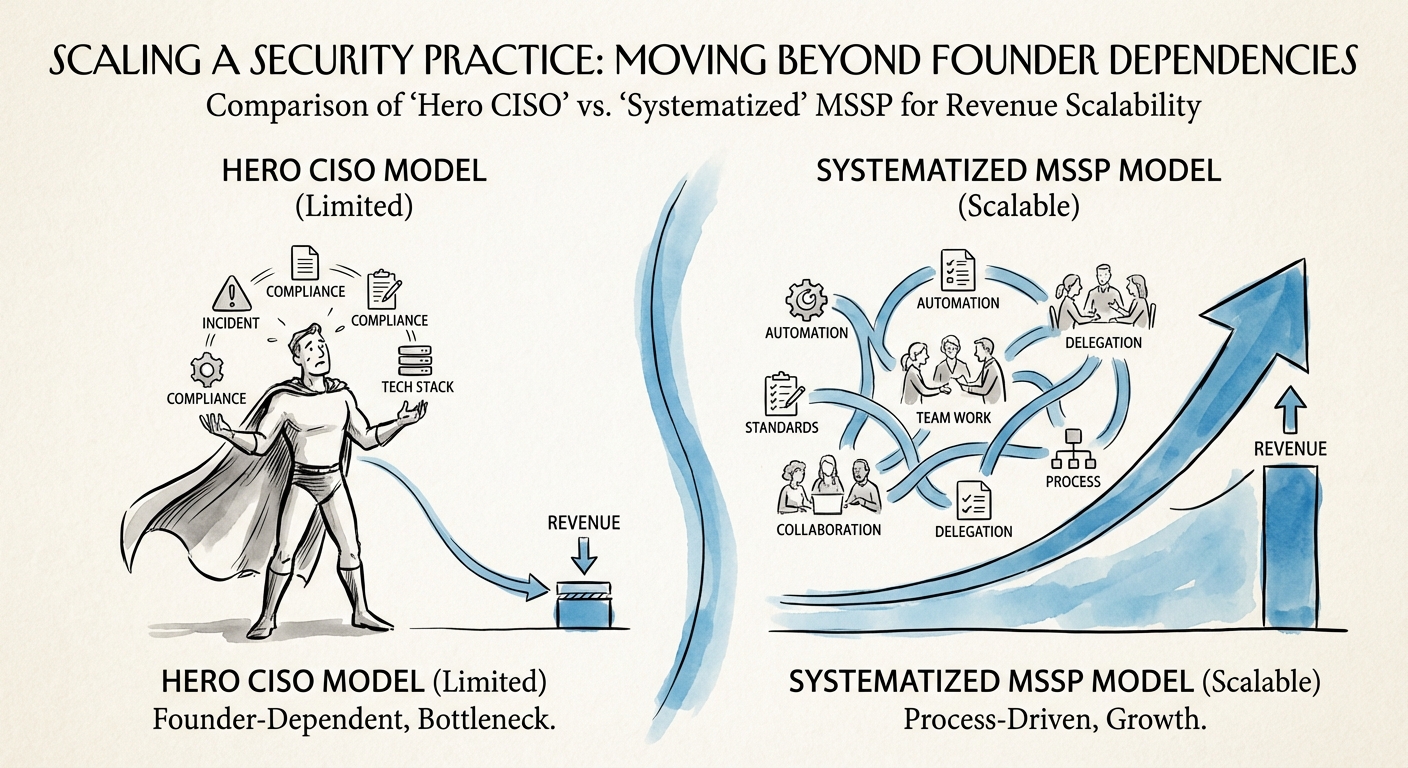
The Playbook: From 'Hero' to 'Head of State'
Scaling beyond founder dependency requires a deliberate transition from being the "Chief Security Architect" to the "CEO." This is an identity shift as much as an operational one.
1. Productize the Service Delivery
Stop selling hours and start selling outcomes. Package your expertise into standardized SKUs—whether that’s a specific "Zero Trust Assessment" framework or a monthly "Compliance Retainer." Define the exact toolset (e.g., CrowdStrike, SentinelOne, Wiz) and refuse to support off-menu configurations. This allows you to hire engineers who can execute the system without needing your intuition.
2. The 'Practice Leader' Hire
The most critical hire you will make is a Practice Leader or VP of Security Operations who has business acumen, not just technical chops. A common mistake is promoting your best engineer, who then struggles to manage P&L. You need a leader who can own the client relationship and the delivery standards. This person is the bridge that allows you to step out of daily delivery.
3. Documenting 'Tribal Knowledge'
You must extract your brain into a knowledge base. Use the Founder Extraction Checklist to identify the 30+ critical processes that currently live in your head. From "How we price a SOC 2 audit" to "How we handle a Sev-1 Ransomware incident," documentation is the only way to transfer trust from a person to a process.
By systematically removing yourself from the critical path, you don't just get your life back—you unlock the premium valuation multiples that institutional buyers pay for scalable, independent platforms.