The New Cost of "Trust Me" in Due Diligence
In 2020, a handshake and a promise of "we follow industry best practices" might have survived a cursory technical review. In 2026, that same approach is a deal-killer. The shift in private equity due diligence has been brutal and swift. Security and compliance are no longer just IT check-the-box exercises; they are valuation levers. According to SRS Acquiom’s 2025 M&A Insights, 97% of dealmakers now cite cybersecurity as receiving the greatest scrutiny in due diligence, surpassing even financial audits in some high-risk verticals.
This scrutiny is driven by a concept we call "Compliance Debt." Just as financial debt must be paid off at closing, reducing the net proceeds to shareholders, Compliance Debt is a liability that buyers deduct from Enterprise Value (EV). If your data room lacks evidence of a mature security posture—documented processes, recent penetration tests, and audit-ready compliance controls—buyers don’t just assume you’re insecure; they assume you require a massive capital injection to become insurable.
Consider the math of a typical middle-market SaaS deal. A buyer identifies that your lack of SOC 2 compliance and undocumented incident response procedures will cost $2M to remediate over 18 months. They don’t just subtract $2M from the purchase price. They apply a risk multiplier—often 1.5x to 2x—to account for the operational distraction and potential integration failure. Suddenly, a few missing folders in your data room have triggered a $3M to $4M valuation haircut. This isn’t theoretical; research indicates that 60% of executives now blame failed deals explicitly on insufficient due diligence findings.
The 5 Documents That Trigger a "Red Flag" Audit
When a Private Equity Operating Partner opens your data room, they aren’t reading every policy. They are scanning for five specific "artifacts of evidence" that serve as proxies for organizational maturity. Missing any one of these triggers a deeper, more invasive "Red Flag" audit.
1. The "Clean" Penetration Test Report (With Remediation Evidence)
Uploading a penetration test from 18 months ago is worse than uploading nothing. It screams negligence. Buyers expect to see a trailing 12-month (TTM) report from a reputable third-party firm. Crucially, they look for the remediation verification. A report showing 12 critical vulnerabilities is a liability; a report showing those same 12 vulnerabilities were patched within 14 days is an asset. It proves you have a functioning remediation process, not just a testing budget.
2. The SOC 2 Type II (or "Gap Analysis" with Roadmap)
If you don’t have a SOC 2 Type II report, you are already trading at a discount compared to compliant peers. However, the "audit ready" proxy can save you. A detailed gap analysis performed by a qualified auditor, accompanied by a board-approved budget and timeline for certification, can mitigate the valuation impact. Buyers fear the unknown; a quantified gap is a manageable risk.
3. The Incident Response "Game Tape"
Policies sit on shelves; logs tell the truth. Buyers want to see evidence that your Incident Response (IR) plan is real. This means Tabletop Exercise (TTX) reports showing who attended (did the CEO show up?), what scenarios were tested (Ransomware? Insider threat?), and what broke. A generic "IR Policy.pdf" downloaded from a template site is a red flag that suggests your team will freeze during a real crisis.
4. Open Source Software (OSS) Scan Reports
With software supply chain attacks rising, buyers are terrified of inheriting "poisoned" codebases. They expect to see automated scans (e.g., Snyk, Black Duck) identifying licensing risks (GPL violations) and security vulnerabilities. A data room without an OSS inventory suggests you don’t know what code is actually running in your product.
5. The Third-Party Risk Management (TPRM) Register
Your security is only as strong as your weakest vendor. A missing TPRM register—documenting which sub-processors hold customer data and their compliance status—is a major integration risk. It implies the buyer will need to audit your entire vendor ecosystem post-close, a cost they will price into the deal.
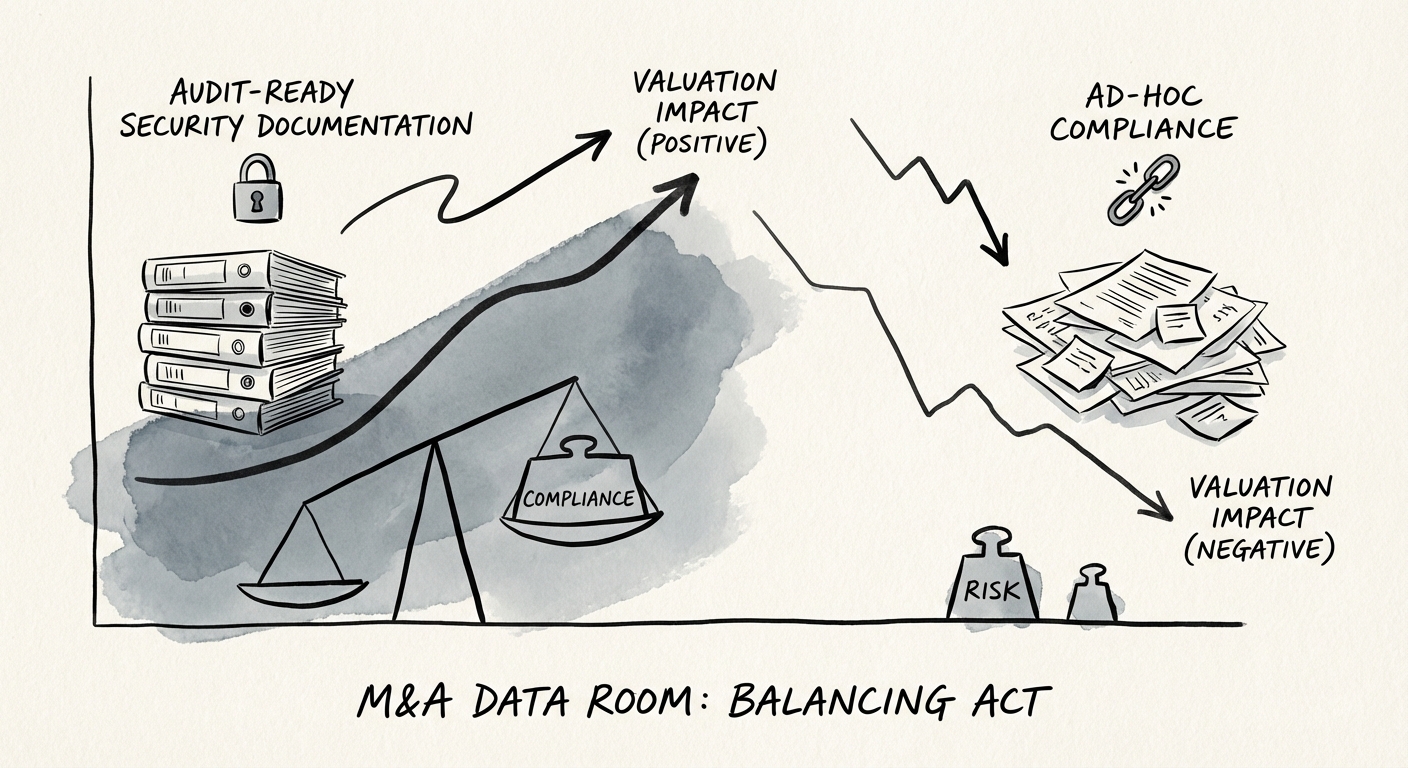
The "Transferability Premium": Structuring Your Data Room for Value
The difference between a 6x and a 10x EBITDA multiple often comes down to "Transferability." Can the buyer step in and run the machine, or is the security posture entirely dependent on a heroic founder or a "guru" CTO? Documented processes command a premium because they de-risk the transition.
To capture this premium, structure your security data room to tell a story of maturity, not just compliance. Organize folders by "Process," "Evidence," and "Governance," rather than just dumping files by year. Create a "Start Here" document that maps your controls to your risks. If you are technically "secure" but your data room looks chaotic, buyers will assume your operations are equally chaotic.
Finally, address the "Technical Debt" narrative head-on. If you have legacy systems that are non-compliant, disclose them in a "Risk Register" with associated mitigation plans. This turns a "gotcha" moment during diligence into a demonstration of competence. As detailed in our guide on security posture assessments, transparency about deficits often builds more trust than a sanitized, unrealistic presentation. Remember, in M&A, silence is expensive. The price of compliance gaps is almost always higher than the cost of documenting them proactively.