Your unmanaged API sprawl is quietly bleeding 15% off your enterprise valuation before the technical due diligence even starts. We see this exact scenario play out every single quarter. Founders and C-suite executives enter a transaction believing their enterprise architecture is a well-oiled machine, only to have a buyer's technical audit reveal a sprawling labyrinth of undocumented, unsecured endpoints. It is not just an engineering headache; it is a massive compliance liability that private equity buyers immediately weaponize to negotiate the purchase price down.
The data behind this oversight is staggering. According to Forrester's 2025 Security Budget Planning API Sprawl Data, only 10% of organizations fully document their APIs. The other 90% are operating blindly, leaving "shadow" or "zombie" APIs exposed to the public internet. These forgotten endpoints bypass standard authentication, lack rate limiting, and serve as a direct conduit to your most sensitive backend databases. I have rebuilt this capability at three different scaling enterprises following failed technical audits, and the pattern is always the same: engineering teams prioritize delivery velocity over governance, leaving a wake of unmanaged technical debt that eventually cripples the company's risk profile.
This lack of visibility translates directly into catastrophic financial risk. The financial implications of a breach have escalated significantly. As detailed in IBM's 2025 Cost of a Data Breach Report, the average cost of a data breach in the United States has surged to $10.22 million, heavily driven by slower detection times and regulatory penalties associated with compromised APIs. When buyers see a lack of API governance during due diligence, they do not just see bad code—they see a ticking $10 million time bomb. For a deeper understanding of what buyers look for, refer to our guide on 10 Red Flags in Technology Due Diligence That Kill Deals.
The False Security of the API Gateway
The most common, and dangerous, misconception I encounter in the C-suite is the belief that purchasing an API gateway constitutes a comprehensive API governance strategy. A gateway is merely a tollbooth; it routes traffic and enforces basic policies on the endpoints it knows about. It does absolutely nothing to protect the shadow APIs spun up by rogue development teams or the zombie endpoints left behind after a legacy system migration. You cannot secure what you cannot see, and gateways are notoriously blind to unmanaged assets.
The threat landscape has evolved far beyond basic perimeter defense. Threat actors are no longer trying to hack through your firewall; they are simply logging in through poorly governed APIs. The reality of this shift is documented in Gartner's 2026 API Security Trends Predictions, which reveals that 99% of organizations have experienced an API security incident in the past year, and that for every human identity, there are approximately 82 machine identities operating within the enterprise. By 2026, organizations will be forced to enforce least-privilege access across millions of these machine identities just to maintain basic operational security.
Furthermore, standard vulnerability management programs are entirely unequipped to handle API sprawl. Gartner's 2026 Cybersecurity Threats and Trends Analysis predicts that through 2026, nonpatchable attack surfaces will grow to include more than half of the enterprise. Undocumented APIs represent the largest and most volatile segment of this nonpatchable surface. If your team cannot dynamically discover, classify, and apply posture management to every single endpoint in runtime, your enterprise integration strategy is structurally flawed. This is a common failure point that we cover extensively in our analysis of The API "Spaghetti Tax": Why Your "Platform" Acquisition Is Just a Monolith in Disguise.

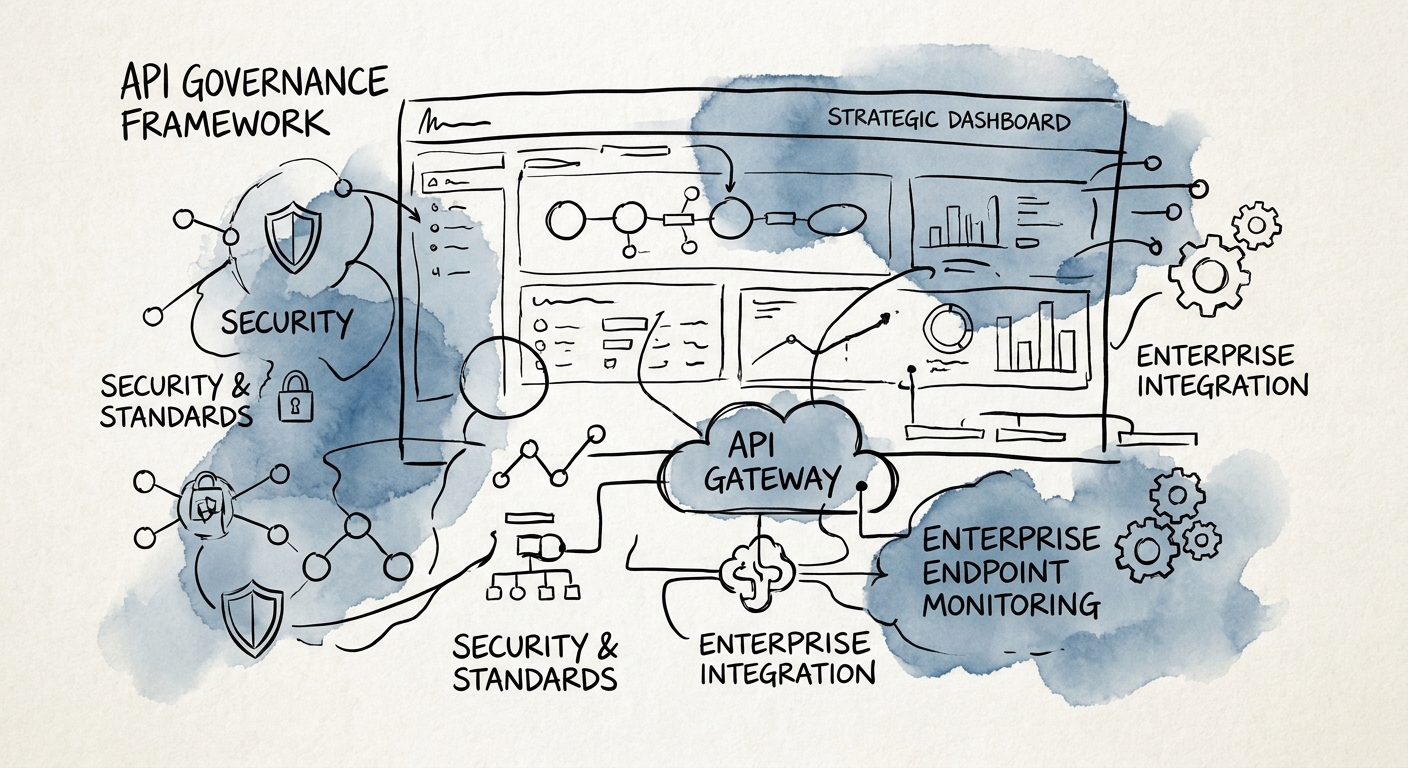
Building a PE-Grade API Governance Framework
To survive modern due diligence and protect your valuation, you must implement an API governance framework that shifts from reactive monitoring to continuous threat exposure management. This requires three foundational pillars: automated continuous discovery, rigorous posture management, and behavioral runtime protection. In our engagements, we require portfolio companies to utilize open-telemetry standards to automatically map every API in the environment—regardless of whether it sits behind a gateway, on-premises, or in the cloud. If an endpoint exists, it must be inventoried, risk-ranked, and assigned a distinct business owner.
The stakes are particularly acute in highly regulated sectors where third-party integrations introduce massive vendor risk. According to Vorlon's 2025 Healthcare Third-Party API Risk Study, average healthcare breach costs reached an unprecedented $10.93 million per incident, with the majority of successful attacks exploiting weak third-party APIs and excessive data-sharing permissions. We see this exact vulnerability pattern across finance, manufacturing, and SaaS. You must enforce zero-trust principles at the API layer, requiring cryptographically verified, sender-constrained tokens for every machine-to-machine interaction.
Ultimately, API governance is not an IT initiative; it is a board-level risk management mandate. Buyers will dissect your API strategy to determine the maturity of your engineering culture and the security of your core intellectual property. By embedding security directly into your CI/CD pipelines and establishing strict deprecation policies for legacy endpoints, you eliminate the shadow attack surface and build a provably secure enterprise. For a comprehensive list of what buyers expect to see in your data room, review our framework on The Security Posture Assessment: A Due Diligence Checklist for Protecting Deal Value.