Unmanaged API integrations aren't just a technical annoyance; they are a hidden capital expenditure liability that will actively drain your EBITDA multiple during private equity due diligence. When evaluating software targets, acquirers don't see your 300 microservices as "agile innovation." They see a chaotic web of undocumented endpoints that will require massive investment to secure and scale.
In our last engagement, we walked into a Series B SaaS company preparing for an exit. Over the course of three years, their "hero" engineering team had spun up dozens of quick integrations to connect their core platform with various CRM and billing tools. By the time we ran the technical audit, they had 342 active APIs, but could only account for the purpose of 115. I have rebuilt this exact architecture at three different portfolio companies, and the pattern is always identical: rapid growth masks architectural rot.
You are not alone in this trap. According to Salt Security's 2023 State of API Security Report, 94 percent of organizations identified shadow APIs running in their environment during routine audits. These "shadow APIs" are endpoints that function entirely outside the purview of the IT and security teams. Furthermore, Enterprise Management Associates' 2023 API Documentation Benchmark reveals that only 10 percent of organizations fully document their application programming interfaces. When you attempt to sell a company where 90 percent of the connective tissue is undocumented, the buyer will heavily discount your valuation to cover the cost of untangling the mess.
The "Hero Architect" Hangover
API sprawl is the direct result of decentralized development without centralized governance. A developer needs to push data to Snowflake, so they write a quick script and open a port. Fast forward five years, and the original developer is gone. The endpoint is still active, but nobody knows who owns it or what breaks if you turn it off. This creates a brittle, unpredictable system that stalls future feature development. If you are preparing for a transaction, you must read 10 Red Flags in Technology Due Diligence That Kill Deals to understand how buyers model the cost of this specific technical debt.
The Due Diligence Discount on Spaghetti Architecture
When private equity firms execute technical due diligence, unmanaged APIs stand out as a glaring, quantifiable risk. The security implications alone are severe enough to derail a transaction. According to Akamai's 2024 API Security Impact Study, the average cost to remediate a single API security breach in the United States reached $591,404. Acquirers know these statistics. They will look at your 200 unmanaged endpoints, model the statistical probability of a breach, and deduct that exposure directly from your enterprise value.
The threat is escalating rapidly as attackers shift their focus from traditional web perimeters to API endpoints. SALT's 2025 Global State of API Security Survey reported that 57 percent of organizations suffered an API-related data breach in the past two years. More alarmingly, of the companies that were breached, 73 percent suffered three or more separate incidents. You cannot convince a buyer that your platform is enterprise-ready when your data flows through unmonitored backdoors.
Beyond the immediate security risk, buyers penalize API sprawl because it represents operational friction. Every new integration takes twice as long to build because engineers must carefully step around the undocumented landmines of the past. IBM's 2026 Threat Intelligence Index found that 31 percent of malicious transactions explicitly targeted shadow APIs. To an acquirer, your platform is not a turn-key asset; it is a remediation project. We dive deeper into how this impacts M&A pricing in The API "Spaghetti Tax": Why Your "Platform" Acquisition Is Just a Monolith in Disguise.
The 90-Day Sprawl Remediation Playbook
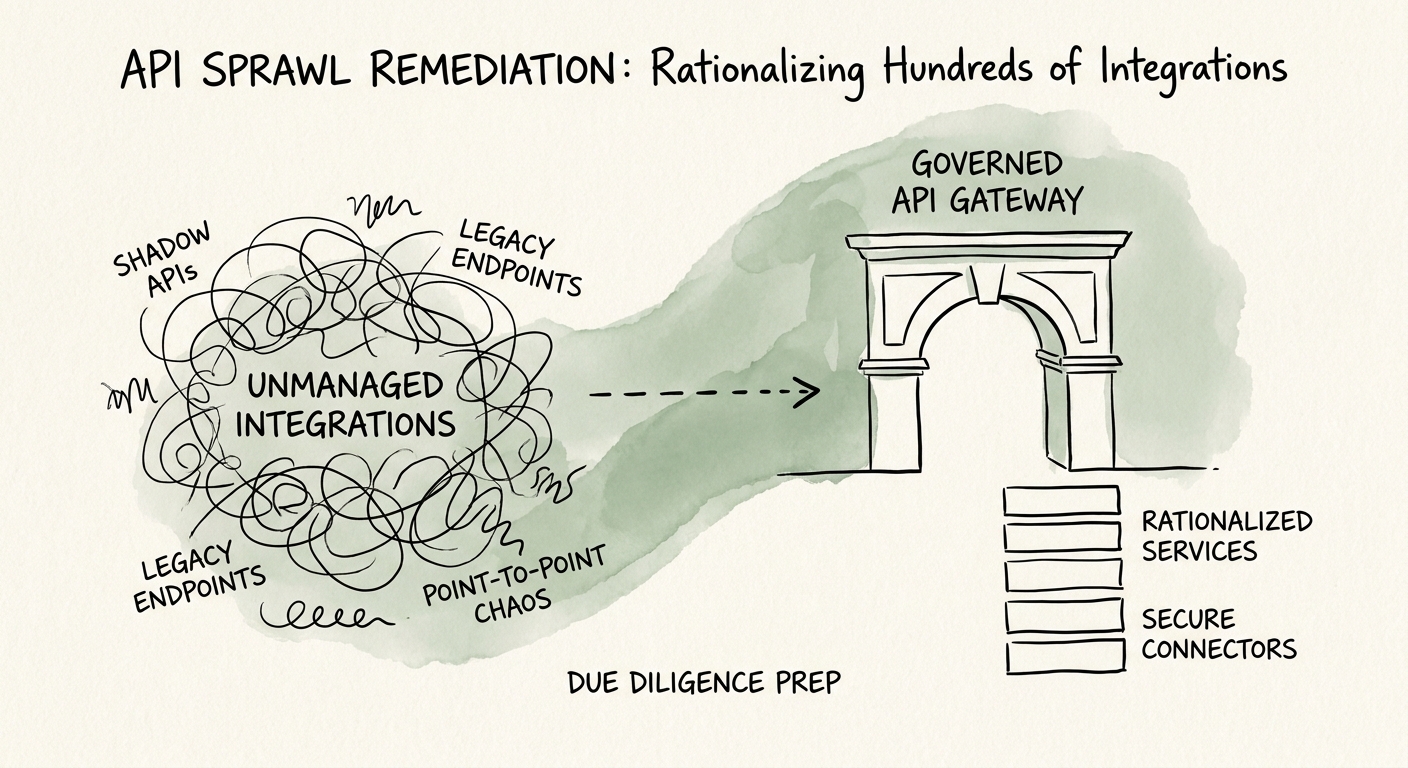
You must move your architecture from chaos to governed predictability before you sign a Letter of Intent. You cannot fake API governance during a code audit. The remediation requires a decisive, 90-day sprint focused on discovery, consolidation, and deprecation.
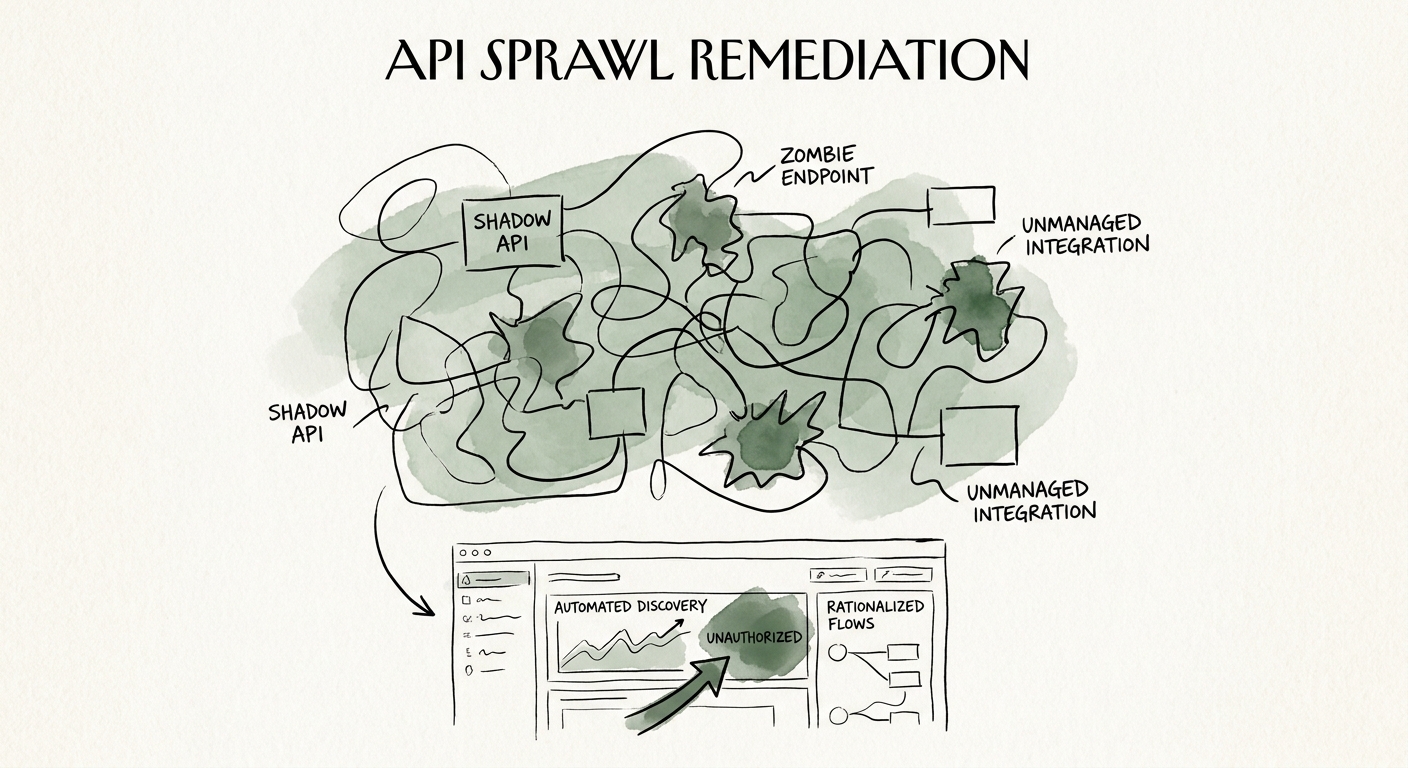
1. Automated Discovery and Inventory
You cannot secure or rationalize what you cannot see. The first step is deploying an API discovery tool to monitor your traffic and map every active endpoint. Gartner's 2025 API Security Predictions forecast that APIs will be the number one attack vector for web applications, largely because organizations lack basic visibility into their own environments. By running automated discovery, you immediately establish a baseline of truth, exposing the zombie APIs that process zero traffic and the shadow APIs that operate outside your gateway.
2. Gateway Consolidation and Policy Enforcement
Once you have a complete inventory, you must route all traffic through a centralized API gateway. This stops the bleeding. By forcing all endpoints to authenticate through a single control plane, you instantly apply universal rate limiting, access controls, and logging. This is the exact maneuver that turns a chaotic engineering culture into a disciplined, scalable machine. See Stop the 'Grand Rewrite': A CEO's Guide to Prioritizing Technical Debt for the precise sequencing of these initiatives.
3. Ruthless Deprecation
The final step is actively shutting down redundant or obsolete endpoints. If an API has not processed legitimate traffic in 60 days and lacks an internal owner, deprecate it. Rationalizing hundreds of unmanaged integrations is not glamorous work, but it is the most lucrative engineering investment you will make prior to an exit. By presenting a clean, governed, and fully documented API ecosystem, you eliminate the buyer's leverage to negotiate a "spaghetti architecture" discount, preserving millions in deal value.